- March 13, 2026
- Tech Stories
Ransomware Disrupts U.S. Municipal Services: Cybersecurity Risks Explained
Ransomware Disrupts U.S. Municipal Services: What Businesses and Cities Must Know Across the United States, ransomware attacks on local governments are becoming more frequent and disruptive. From payment portals to…
- March 11, 2026
- Tech Stories
AkzoNobel Data Breach: 170GB of Data Stolen in Anubis Ransomware Attack
AkzoNobel Data Breach – 170GB of Data Stolen in Anubis Ransomware Attack Introduction: A Cyberattack on One of the World’s Largest Paint ManufacturersCyberattacks are no longer limited to tech companies…
- March 10, 2026
- Tech Stories
Suspected Chinese Hackers Breach FBI Surveillance Network: What the 2026 Cyberattack Means for U.S. Security
Suspected Chinese Hackers Breach FBI Surveillance Network: What the Cyberattack Means for U.S. Security Cybersecurity incidents involving government systems rarely remain confined to technical circles. When a breach occurs inside…
- March 5, 2026
- Tech Stories
Wynn Resorts Confirms Employee Data Breach Affecting 800,000
Wynn Resorts Confirms Employee Data Breach: Businesses and Employees Should Know The Wynn Resorts data breach has quickly become one of the most discussed cybersecurity incidents of 2026. When Wynn…
- March 2, 2026
- Tech Stories
Malaysia Airlines Ransomware Attack: Qilin Claim Explained
Malaysia Airlines Ransomware Attack: What North Carolina Businesses Should Know About the Qilin Ransomware Claim In late February 2026, cybersecurity monitoring platforms began reporting that Malaysia Airlines had been listed…
- February 27, 2026
- Tech Stories
CarGurus Data Breach 2026: 1.7M Records Stolen by ShinyHunters
CarGurus Data Breach: 1.7M Records Stolen — What North Carolina Users and Dealers Need to Know In February 2026, headlines began circulating about a major CarGurus data breach, with claims…
- February 25, 2026
- Tech Stories
Poland Energy Sector Cyber Incident: OT/ICS Security Lessons for North Carolina Energy Providers
Poland Energy Sector Cyber Incident: What North Carolina Energy Leaders Must Learn from a Coordinated OT/ICS Cyber Attack Critical infrastructure attacks no longer make headlines simply because they occur. They…
- February 24, 2026
- Tech Stories
Washington Hotel Ransomware Attack: What Businesses in NC Should Know
Washington Hotel Chain Hit by Ransomware: What North Carolina Businesses Should Learn from the Japan Cyberattack Cyberattacks no longer make headlines only when banks or technology giants are targeted. Increasingly,…
- February 17, 2026
- Tech Stories
Minnesota DHS Data Breach Explained: What Happened, Who Was Affected, and Why It Matters
Apple Pushes Emergency iPhone Update after spyware attack. When Apple issues a routine software update, most users casually tap “Install Tonight” and move on. But when your iPhone displays an…
- February 10, 2026
- Tech Stories
Minnesota DHS Data Breach Explained: What Happened, Who Was Affected, and Why It Matters
Minnesota DHS Breach: A Closer Look at What Happened and Why It Matters Nationwide Data breaches are no longer isolated incidents limited to private corporations or tech companies. Increasingly, public…
- February 9, 2026
- Tech Stories
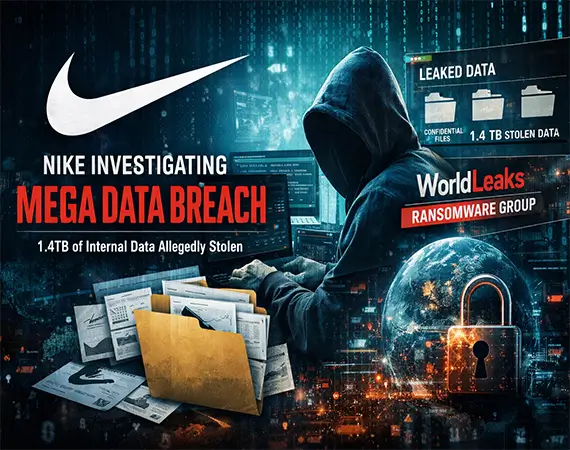
Nike Investigates Mega Cybersecurity Breach Involving 1.4TB of Internal Data
Nike Investigating Mega Data Breach — 1.4TB of Internal Files Allegedly Stolen Nike, one of the world’s most recognizable brands, is currently investigating what could become one of the most…
- February 3, 2026
- Tech Stories
Crunchbase Hacked by ShinyHunters: 2026 Data Breach Explained
Crunchbase Hacked by ShinyHunters: A Deep Dive into the 2026 Data Breach and Its Impact on North Carolina Businesses In 2026, reports that Crunchbase had been hacked by the cybercrime…
Rate this page