Your Kid’s Gaming Rig Could Survive a Cyberattack.
Your Kid’s Gaming Rig Could Survive a Cyberattack. Can Your Office? Walk into your home one evening, and you’ll likely [...]
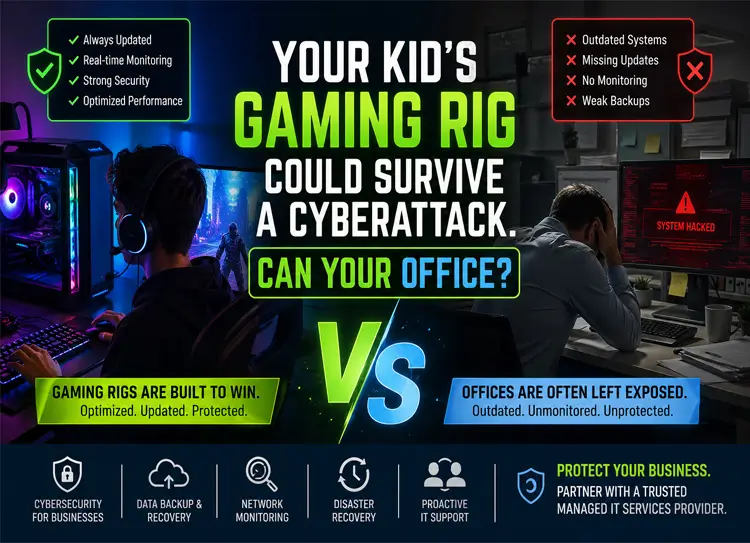
Your Kid’s Gaming Rig Could Survive a Cyberattack. Can Your Office? Walk into your home one evening, and you’ll likely [...]
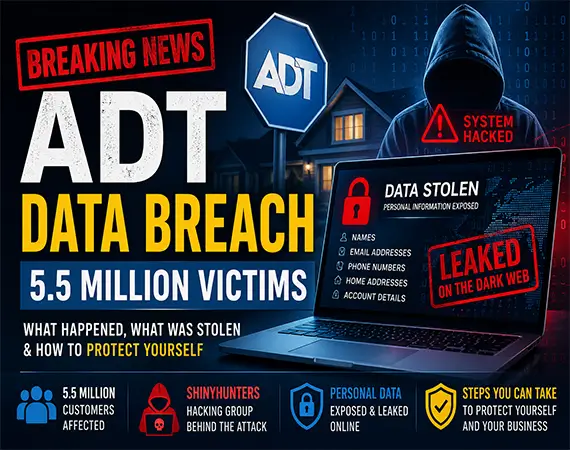
Massive ADT Data Breach (5.5 Million Victims): What Businesses Must Learn in 2026 Introduction: Another Wake-Up Call for Cybersecurity in [...]
Why Do Modern Ransomware Attacks Now Happen in Under 24 Hours? Most modern ransomware attacks now unfold in 4 to [...]

What Is IT Spring Cleaning for Businesses? (2026 Checklist to Improve Security & Performance) For most small and mid-sized businesses, [...]

What Happened in the Northern Ireland School Cyberattack (C2k) and Why Schools & SMB Networks Are Prime Ransomware Targets? A [...]

Rockstar Games Ransomware Attack (ShinyHunters): Why Third-Party Tools Are the Weakest Link in Cybersecurity The Rockstar Games ransomware attack in [...]

April Fools Jokes Are Over, but These Scams Aren’t Fun Pranks April Fools’ Day has always been about harmless fun—office [...]

TELUS Digital Data Breach 2026: What Happened, Impact & Key Lessons for Businesses In early 2026, the cybersecurity world was [...]
How a Cup of Coffee Can Take Down Your Entire Business It starts like any other morning. You grab a [...]

Iran-Linked Cyber Threats Are Escalating Globally: What Businesses Need to Know “Iran is no longer just a regional cyber threat—it’s [...]

LA Metro Cyber Incident Disrupts Services: What Happened and What It Means In March 2026, one of the largest public [...]
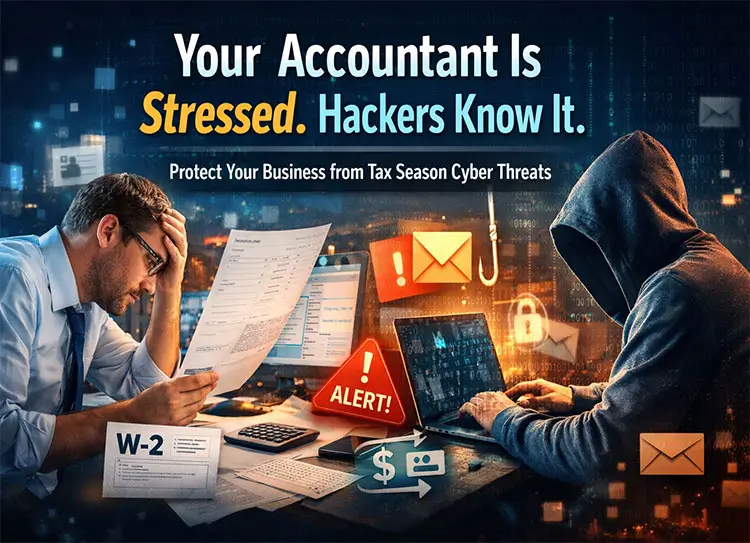
Your Accountant Is Stressed. Hackers Know It. It’s March. Deadlines are closing in. Emails are piling up. Financial documents are [...]