Suspected Chinese Hackers Breach FBI Surveillance Network: What the Cyberattack Means for U.S. Security
Cybersecurity incidents involving government systems rarely remain confined to technical circles. When a breach occurs inside a critical law-enforcement system—particularly one used for surveillance and national security—the implications extend far beyond the organization itself.
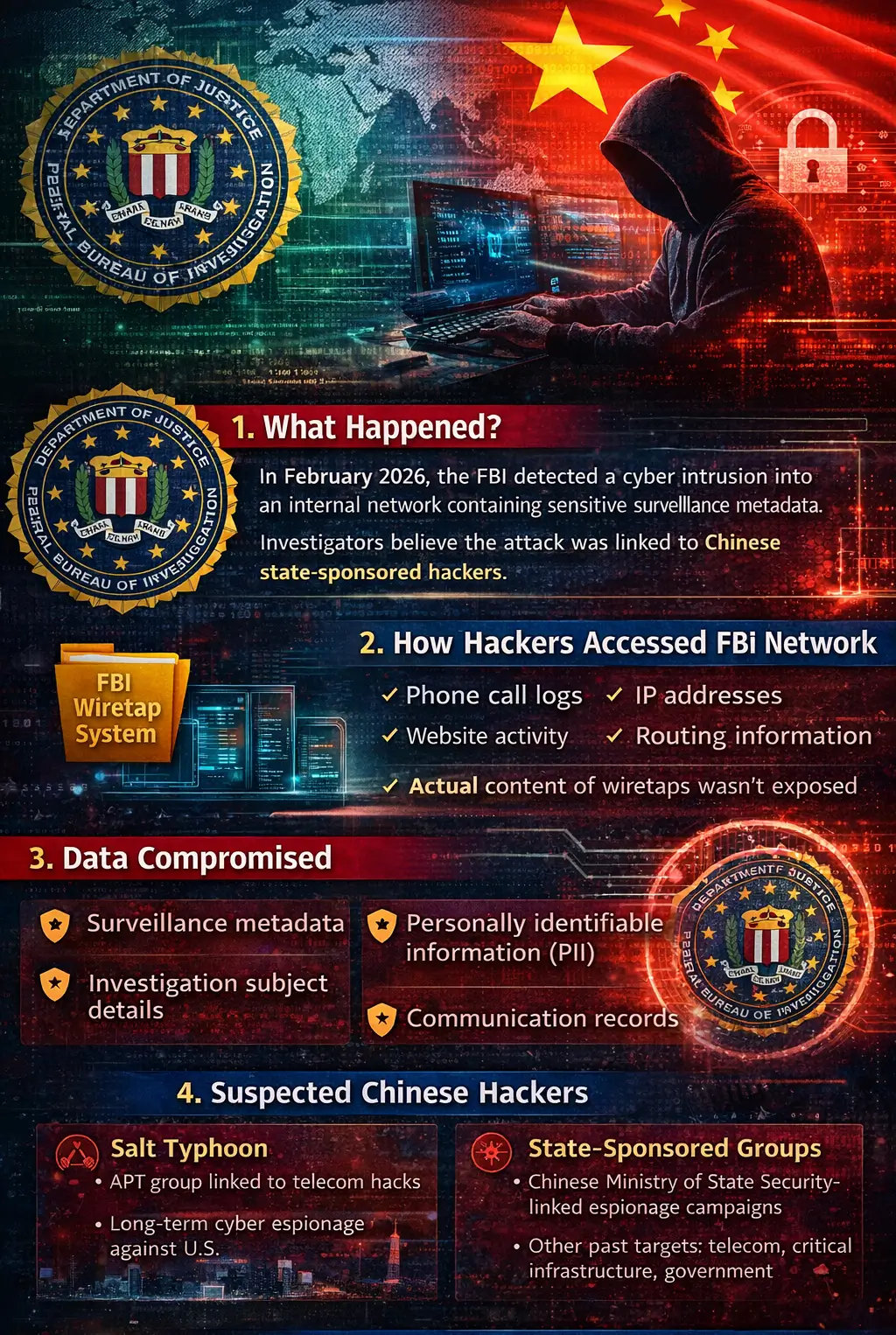
In early 2026, the United States government began investigating what is now widely described as the FBI surveillance network breach, a cyber incident suspected to involve Chinese state-sponsored hackers infiltrating an internal surveillance system used by federal investigators.
The FBI cyberattack 2026 quickly became a major national security concern. Reports indicated that attackers accessed an internal database connected to court-authorized surveillance programs. While the full scope of the FBI cybersecurity breach remains under investigation, the incident highlights the growing threat of nation-state cyberattacks targeting government infrastructure.
For organizations and businesses across the United States—including those in North Carolina—this incident provides important lessons about modern cyber threats. If highly secured federal systems can be targeted, private organizations must take cybersecurity preparedness even more seriously.
In this article, we examine what happened during the FBI surveillance system cyberattack, what systems were affected, the suspected involvement of Chinese hackers, and what businesses can learn from this evolving cyber threat landscape.
What Happened in the FBI Cyberattack
The FBI cyberattack 2026 was first discovered after federal investigators detected suspicious activity within an internal system used for managing surveillance data.
The FBI investigation cyber intrusion began when cybersecurity teams noticed unusual access patterns and potential unauthorized queries inside a database tied to federal wiretap operations. Initial assessments suggested that attackers may have gained access to an internal network that stores metadata collected through surveillance programs.
According to multiple reports, investigators suspect Chinese hackers targeting the FBI network, potentially linked to long-running cyber espionage campaigns conducted by Chinese intelligence groups.
While details are still emerging, several facts have been widely reported:
- Suspicious network activity was detected in February 2026
- Attackers accessed a database connected to surveillance monitoring programs
- The breach involved law-enforcement-sensitive information rather than classified intelligence
- U.S. authorities suspect China-linked cyber espionage actors
The incident has since been described as a possible government surveillance infrastructure attack, highlighting the increasing willingness of nation-state hackers to target law enforcement systems.
Although the breach did not reportedly expose the actual content of intercepted communications, the surveillance metadata breach could still provide valuable intelligence to foreign adversaries.
How Hackers Accessed the Surveillance Network
To understand the impact of the FBI wiretap system hack, it is important to understand the role of the system that was targeted.
The compromised network reportedly supports the management of surveillance operations authorized under federal law. These systems help investigators track communication metadata associated with court-approved monitoring activities.
The database reportedly supports:
- Court-authorized wiretap programs
- Foreign Intelligence Surveillance Act (FISA) warrants
- Monitoring of suspects connected to criminal investigations
- Communication tracking used in counterintelligence operations
This infrastructure is commonly described as part of the FBI wiretap system, which supports digital monitoring capabilities used in law enforcement investigations.
However, reports indicate the compromised system stores metadata rather than message content. The difference is important.
Metadata includes information such as:
- Phone call logs
- IP address records
- Website activity
- Network routing data
- Communication timestamps
While the content of phone calls or emails may not have been stored in this system, metadata can still reveal significant intelligence about individuals, organizations, or investigations.
For example, metadata can show:
- who communicated with whom
- when communications occurred
- patterns of contact between suspects
- location indicators
This type of data is extremely valuable in intelligence gathering.
The incident therefore represents a FBI wiretap system breach, potentially exposing sensitive investigative information.
What Data May Have Been Compromised
One of the biggest questions surrounding the FBI cybersecurity breach is what information the attackers actually obtained.
While authorities have not disclosed the complete scope of the breach, cybersecurity experts believe several types of information may have been exposed.
Possible compromised data includes:
Surveillance Metadata
Attackers may have accessed metadata associated with surveillance programs, including communication logs and network traffic records.
Personally Identifiable Information (PII)
Some investigative records may include identifying details related to individuals being monitored.
Investigation Subject Details
Metadata connected to law enforcement investigations could reveal information about ongoing cases.
Communication Records
Information such as timestamps, phone numbers, or digital identifiers may have been exposed.
Although the affected database reportedly contained law-enforcement-sensitive data rather than classified intelligence, the exposure still raises concerns.
Foreign intelligence agencies can often combine metadata from multiple breaches to construct detailed intelligence profiles.
This is why the impact of the FBI surveillance system breach is being taken seriously by national security officials.
The Role of Chinese State-Sponsored Hackers
Investigators suspect the intrusion may have been carried out by Chinese state-sponsored hackers, a group frequently associated with long-term cyber espionage campaigns against the United States.
Cybersecurity analysts often categorize these attackers as Advanced Persistent Threats (APTs).
An APT China cyber campaign typically involves:
- long-term network infiltration
- stealthy data collection
- persistence within systems
- intelligence gathering rather than immediate disruption
One group frequently mentioned in connection with recent cyber espionage activities is the Salt Typhoon hacking group.
This group has previously been linked to attacks targeting:
- telecommunications infrastructure
- government agencies
- critical national infrastructure
Experts believe groups like Salt Typhoon may operate with support from Chinese intelligence agencies, particularly the Ministry of State Security (MSS).
If confirmed, the China suspected FBI hack would represent another example of U.S. government cyber espionage by foreign adversaries.
These operations are typically designed not to destroy systems, but to quietly gather intelligence.
Why Surveillance Systems Are Prime Cyber Targets
Government surveillance infrastructure is among the most valuable targets for foreign intelligence services.
A government surveillance infrastructure attack can provide insight into how law enforcement monitors criminal networks, spies, and foreign actors.
Attackers may target surveillance systems to:
Monitor Investigations
If attackers can access surveillance databases, they may identify individuals or organizations currently under investigation.
Identify Intelligence Sources
Metadata can sometimes reveal the identity of confidential informants or intelligence assets.
Track Government Operations
Access to surveillance systems may reveal how law enforcement conducts monitoring operations.
Gather Intelligence
Even metadata alone can provide insight into national security activities.
For these reasons, systems used for foreign intelligence surveillance warrants are particularly attractive to nation-state attackers.
Understanding why government surveillance networks are targeted helps explain the seriousness of this breach.
FBI’s Response to the Breach
After detecting suspicious activity, the FBI initiated an immediate cybersecurity investigation.
The agency reportedly took several steps to contain the intrusion.
These actions included:
- identifying compromised systems
- conducting forensic cybersecurity analysis
- notifying government oversight authorities
- implementing additional security measures
Members of Congress were also briefed on the situation as part of the government’s oversight responsibilities.
The FBI investigation cyber intrusion is ongoing, and authorities are working to determine:
- how the attackers gained access
- how long they remained inside the network
- what data may have been accessed or removed
Investigators are also examining whether the breach was connected to a broader cyber espionage campaign targeting U.S. infrastructure.
What This Means for Global Cybersecurity
The FBI surveillance network breach highlights a growing trend in international cyber conflict: nation-state cyber espionage targeting government infrastructure.
Over the past decade, cybersecurity experts have observed increasing cyber activity linked to foreign intelligence agencies.
These campaigns often target:
- telecommunications providers
- defense contractors
- government networks
- critical infrastructure
The suspected U.S. cybersecurity threat from China has been a growing concern for policymakers and security analysts.
Chinese cyber operations have previously been linked to:
- intellectual property theft
- espionage campaigns
- infrastructure infiltration
The Chinese hackers FBI network intrusion represents another example of how geopolitical competition increasingly extends into cyberspace.
As global tensions rise, cybersecurity will remain a critical component of national security strategy.
Cybersecurity Lessons for Businesses in North Carolina
Although the FBI wiretap system breach involves a federal agency, the lessons extend far beyond government systems.
Businesses across the United States—including those in North Carolina cities like Raleigh, Durham, Cary, and Chapel Hill—face similar cyber threats.
In fact, small and mid-sized organizations are increasingly targeted because they often have fewer cybersecurity defenses.
Here are several lessons businesses should take from this incident.
Even Advanced Security Systems Can Be Breached
If attackers can infiltrate systems used by federal investigators, it demonstrates the sophistication of modern cyber threats.
Businesses should assume that cyber attackers will attempt to bypass traditional security defenses.
Nation-State Threats Are Increasing
Many organizations assume they are only targeted by criminal hackers.
However, nation-state cyberattack tactics are increasingly used in broader cyber campaigns that can impact private organizations.
Continuous Network Monitoring Is Critical
Early detection played an important role in identifying the FBI surveillance system cyberattack.
Organizations should invest in:
- threat detection systems
- security monitoring tools
- real-time network analysis
Identity and Access Management Matters
Many cyber intrusions begin with compromised credentials.
Strong authentication measures such as multi-factor authentication (MFA) can significantly reduce risk.
Incident Response Planning Is Essential
Cybersecurity incidents are no longer a matter of if, but when.
Organizations must develop incident response plans that allow them to respond quickly and minimize damage.
The Growing Cybersecurity Challenge Ahead
The suspected Chinese hackers FBI network breach is a reminder that cyber threats are evolving rapidly.
Modern cyber conflicts no longer involve only criminal groups seeking financial gain. Increasingly, they involve nation-state espionage campaigns designed to gather intelligence and gain strategic advantage.
As digital systems become more interconnected, protecting sensitive data will remain one of the most critical challenges for governments, businesses, and organizations alike.
For businesses in North Carolina and across the United States, staying informed about emerging cyber threats is the first step toward building stronger defenses.
Cybersecurity is no longer just an IT issue—it is a fundamental component of organizational resilience in the digital age.
Frequently Asked Questions (FAQs)
- What is the FBI surveillance network breach?
The FBI surveillance network breach refers to a suspected cyber intrusion into an internal FBI system used to manage surveillance metadata related to court-authorized investigations. In early 2026, federal investigators detected suspicious activity within a database that supports surveillance monitoring operations.
Authorities suspect Chinese state-sponsored hackers may have accessed parts of the system containing law-enforcement-sensitive information such as communication metadata and investigative records. The incident triggered a large-scale FBI investigation into the cyber intrusion.
- What data was exposed in the FBI cyberattack?
Reports suggest the breach involved a surveillance metadata database, rather than the content of intercepted communications.
Possible exposed information includes:
- Phone call logs
- IP addresses and internet activity records
- Communication timestamps
- Routing data and metadata
- Potential personally identifiable information (PII) related to investigations
Although the compromised system did not store the actual content of calls or emails, the surveillance metadata breach could still provide valuable intelligence to foreign actors.
- How did Chinese hackers breach the FBI surveillance network?
Investigators are still determining how Chinese hackers breached the FBI network, but cybersecurity experts believe the attack may have involved tactics commonly used by Advanced Persistent Threat (APT) groups.
These tactics can include:
- exploiting system vulnerabilities
- credential theft or phishing attacks
- supply chain compromise
- long-term stealth access to government networks
Groups linked to Chinese cyber espionage, such as the Salt Typhoon hacking group, are known for conducting long-term cyber espionage campaigns against government infrastructure.
- Why are government surveillance systems targeted by hackers?
Government surveillance systems are considered high-value targets for cyber espionage.
Attackers may target them to:
- monitor ongoing investigations
- identify intelligence sources or confidential informants
- track national security operations
- gather intelligence on law enforcement capabilities
A successful government surveillance infrastructure attack can provide adversaries with insights into how authorities monitor criminal networks or foreign threats.
- What is the impact of the FBI surveillance system breach?
The impact of the FBI surveillance system breach goes beyond a single agency.
Potential consequences include:
- exposure of sensitive investigative metadata
- intelligence advantage for foreign adversaries
- increased geopolitical cyber tensions
- potential risks to national security operations
More broadly, the incident highlights the growing risk of nation-state cyberattacks targeting government networks.
- What can businesses learn from the FBI cyberattack?
The FBI cyberattack 2026 demonstrates that even highly secured government networks can be targeted by sophisticated attackers.
Businesses should take several lessons from this incident:
- cyber threats are becoming more sophisticated
- organizations must continuously monitor networks
- strong identity and access management is critical
- cybersecurity incident response planning is essential
Companies should also recognize that cyber espionage campaigns increasingly target private organizations, particularly those connected to government contracts, technology, or infrastructure.
How Computerbilities Helps North Carolina Businesses Stay Protected
Cybersecurity incidents like the FBI cybersecurity breach are a reminder that organizations of all sizes must take digital threats seriously.
At Computerbilities, we help businesses across North Carolina—including Raleigh, Cary, Durham, Wake Forest, Apex, and Chapel Hill—strengthen their cybersecurity posture and defend against evolving threats.
Our managed IT and cybersecurity services are designed to protect organizations from the same types of attacks seen in major cyber incidents.
Managed IT Services
Our Managed IT Services provide continuous monitoring and proactive support to keep your systems secure and operational.
Key services include:
- 24/7 network monitoring
- proactive threat detection
- system updates and patch management
- infrastructure security management
This ensures vulnerabilities are identified before attackers can exploit them.
Advanced Cybersecurity Protection
Modern cyber threats require modern defenses.
Computerbilities provides comprehensive cybersecurity solutions including:
- endpoint protection and threat detection
- advanced firewall security
- email security and phishing protection
- ransomware protection systems
- identity and access management solutions
These tools help organizations defend against nation-state cyberattack techniques and sophisticated hacker groups.
Compliance and Risk Management
Many industries must comply with cybersecurity standards and data protection regulations.
Computerbilities helps organizations manage compliance with frameworks such as:
- HIPAA
- PCI DSS
- cybersecurity best practices for regulated industries
Our team ensures your business maintains strong cybersecurity governance while reducing risk.
Incident Response and Disaster Recovery
Cyber incidents can occur unexpectedly. A rapid response is essential to minimize disruption.
Our team helps businesses implement:
- incident response strategies
- backup and disaster recovery solutions
- ransomware recovery plans
- business continuity planning
These measures ensure your organization can recover quickly if a cyber incident occurs.
Final Thoughts
The suspected Chinese hackers FBI network breach highlights the evolving nature of cyber threats in today’s interconnected world.
Nation-state cyber espionage, advanced hacking groups, and increasingly sophisticated attack techniques are becoming a reality for governments and businesses alike.
For organizations in North Carolina, strengthening cybersecurity defenses is no longer optional—it is essential for protecting data, operations, and customer trust.
By partnering with experienced IT providers like Computerbilities, businesses can stay ahead of emerging cyber threats and build resilient systems capable of withstanding modern cyberattacks.
If you want to ensure your business is protected from today’s most advanced cyber threats, Computerbilities is here to help.