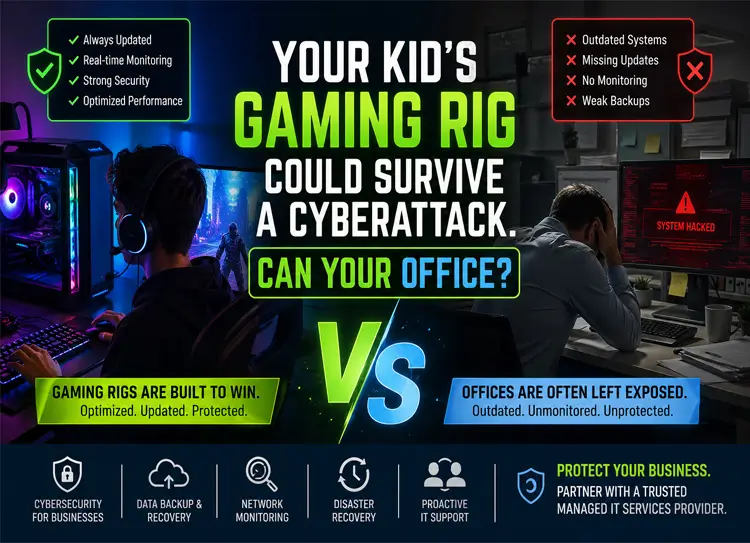
Your Kid’s Gaming Rig Could Survive a Cyberattack. Can Your Office?
Walk into your home one evening, and you’ll likely find your kid immersed in a high-performance gaming setup—RGB lights glowing, ultra-fast processors humming, and every system running at peak efficiency.
Now walk into your office.
Different story, right?
Slow computers. Outdated software. Random glitches. Maybe even that one employee who “just restarts the system and hopes for the best.”
Here’s the uncomfortable truth:
👉 Your kid’s gaming PC is probably more secure, better optimized, and more resilient to cyberattacks than your business IT environment.
And in today’s threat landscape, that’s not just embarrassing—it’s dangerous.

Why Gaming PCs Are Surprisingly More Secure
At first glance, it sounds absurd. How could a gaming PC outperform a business network?
But when you break it down, it makes perfect sense.
⚡ 1. Constant Updates and Patching
Gamers obsess over performance. That means:
- Regular software updates
- GPU driver upgrades
- Security patches installed immediately
Meanwhile, many businesses delay updates because:
- “It might break something”
- “We’ll do it later”
👉 Result: Unpatched vulnerabilities = open doors for hackers
🔍 2. Real-Time Monitoring
Gamers track:
- CPU usage
- Network latency
- System health
They notice problems instantly.
Businesses?
- Often discover issues after damage is done
👉 This is where network security monitoring becomes critical.
🛡️ 3. Built-In Security Awareness
Gamers:
- Avoid suspicious downloads
- Use anti-cheat and anti-malware tools
- Protect accounts with MFA
Businesses:
- Employees click phishing links
- Weak passwords
- No multi-factor authentication
👉 This creates massive gaps in office cybersecurity
⚙️ 4. Performance Optimization Mindset
Gamers constantly:
- Upgrade hardware
- Remove bottlenecks
- Optimize speed
Businesses often:
- Keep outdated systems for years
- Ignore slow performance
👉 Result: Outdated office systems = both security risk AND productivity killer
Why Businesses Are More Vulnerable Than Ever
Now let’s flip the perspective.
🔐 1. Unpatched Vulnerabilities Everywhere
If your systems aren’t updated regularly:
- Hackers exploit known weaknesses
- Automated attacks scan for outdated systems
👉 This is one of the biggest failures in cyberattack prevention strategies
🧩 2. The “Technology Accumulation Problem”
Over time, businesses:
- Add tools
- Install software
- Integrate systems
But rarely remove or optimize anything.
👉 Result:
- Messy infrastructure
- Security gaps
- Poor performance
🛑 3. Reactive IT Support (Big Mistake)
Most SMBs rely on:
- “Break-fix” IT support
- Calling someone only when things go wrong
Gamers fix issues instantly.
Businesses wait.
👉 That delay can cost:
- Thousands in downtime
- Data loss
- Customer trust
💾 4. Weak or Nonexistent Backup Systems
Here’s a scary stat:
👉 Nearly 68% of SMBs don’t have a proper disaster recovery plan
That means:
- No reliable data backup solutions
- No business continuity planning
One ransomware attack = game over
The Hidden Cost of Poor IT Infrastructure
Let’s talk money.
Because this isn’t just about cybersecurity—it’s about profit.
📉 Productivity Loss
Slow systems = wasted time
Even 10 minutes per employee per day = huge annual loss
⏳ IT Downtime Impact
System crash = entire team stops working
👉 Downtime costs small businesses thousands per hour
🔄 Technology Bottlenecks
Old systems:
- Slow down workflows
- Reduce efficiency
- Increase frustration
💰 Hidden IT Costs
You may not see it, but you’re paying for:
- Inefficiency
- Repairs
- Lost opportunities
👉 Cybersecurity + performance = business success
Cybersecurity Risks You Can’t Ignore
Here’s what your business is up against:
- Phishing attacks
- Ransomware
- Data breaches
- Insider threats
Without:
- Endpoint security
- MFA
- Network monitoring
👉 You’re already exposed—you just don’t know it.
Quick Self-Assessment: Is Your Office at Risk?
Ask yourself:
- Are all your systems regularly updated?
- Do you have multi-factor authentication enabled?
- Are your backups tested and reliable?
- Do you monitor your network 24/7?
- Do you know your system performance metrics?
If you hesitated on even one…
👉 Your business is vulnerable.
🚀 How Managed IT Services Solve This Problem
This is where managed IT services change everything.
Instead of waiting for problems:
- Issues are detected early
- Fixed before impact
🔐 Advanced Cybersecurity Solutions
- Continuous monitoring
- Threat detection
- Data loss prevention
☁️ Cloud Solutions for Businesses
- Secure data storage
- Scalable infrastructure
- Remote accessibility
- Automated backups
- Fast recovery
- Disaster recovery planning
⚙️ IT Infrastructure Optimization
- Faster systems
- Better performance
- Reduced downtime
👉 In short:
Your business starts operating like a high-performance system—just like a gaming rig.
Why This Matters for North Carolina Businesses
If you’re in:
You’re part of a growing, competitive business environment.
Cyber threats are increasing, and SMBs are prime targets.
👉 Investing in cybersecurity for businesses in North Carolina isn’t optional anymore—it’s essential.
How Computerbilities Helps Your Business
At Computerbilities, we specialize in helping SMBs transform their IT from reactive to proactive.
💼 Our Services Include:
- Managed IT services in North Carolina
- IT support for businesses
- Cybersecurity solutions
- Network security monitoring
- Data backup and recovery
- Disaster recovery planning
🔍 What Makes Us Different?
- Proactive approach
- Local expertise (Raleigh, Cary, Durham)
- Tailored IT strategies
- Fast response times
🎯 Our Goal:
👉 To make your business IT as secure, fast, and reliable as a high-performance gaming system.
📞 Ready to Protect Your Business?
Don’t wait for a cyberattack to expose your weaknesses.
👉 Get a FREE IT assessment today
👉 Schedule a cybersecurity audit
👉 Talk to a trusted managed IT services provider
FAQs
- Why is my business more vulnerable than a gaming PC?
Because businesses often delay updates, lack monitoring, and rely on outdated systems, while gaming PCs are constantly optimized and updated.
- What is proactive IT support?
Proactive IT support identifies and fixes issues before they impact your business, unlike reactive support which only responds after problems occur.
- How do managed IT services improve cybersecurity?
They provide continuous monitoring, regular updates, threat detection, and data protection strategies to prevent cyberattacks.
- What is a disaster recovery plan?
It’s a strategy that ensures your business can recover data and resume operations quickly after a cyberattack or system failure.
- How often should businesses update their systems?
Ideally, updates should be automatic and continuous to avoid unpatched vulnerabilities.
- Why is data backup important?
Without backups, a cyberattack or system failure can result in permanent data loss and business disruption.
- What industries are most at risk?
Small and medium businesses across all industries are prime targets because they often lack strong cybersecurity defenses.
✅ Final Takeaway
Your kid’s gaming rig isn’t just built for fun—it’s built for performance, speed, and security.
Your business should be too.
👉 Because in today’s world:
If your systems aren’t optimized and protected, your business is at risk.