What Happened in the Northern Ireland School Cyberattack (C2k) and Why Schools & SMB Networks Are Prime Ransomware Targets?
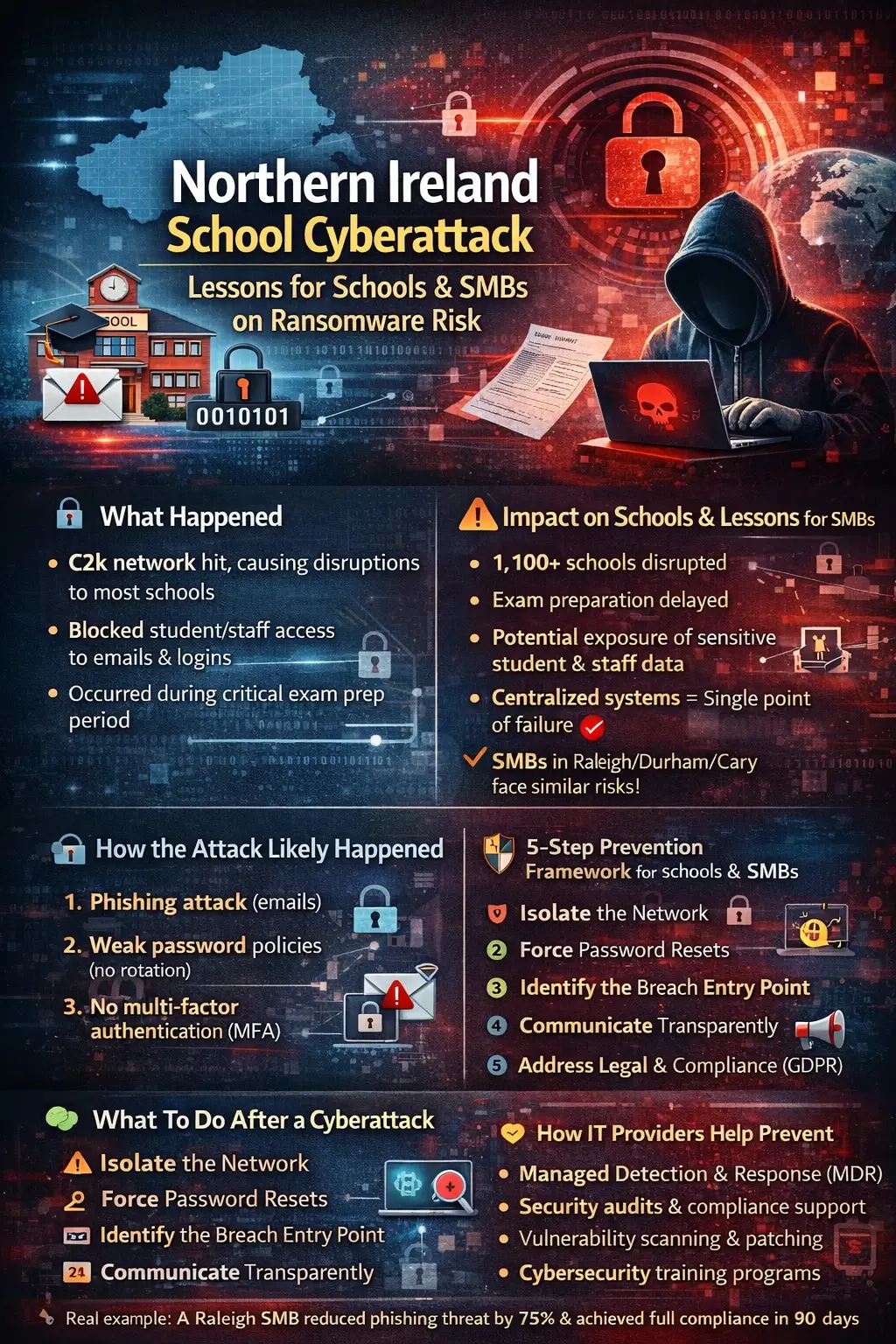
A major Northern Ireland school cyberattack targeting the C2k network disrupted IT systems across hundreds of schools, forcing password resets, limiting access to critical platforms, and impacting exam preparation timelines. Incidents like this aren’t isolated—they reflect a growing trend: education and small-to-mid-sized business (SMB) networks are now among the top 3 ransomware targets globally.
For organizations in Raleigh, Durham, Cary, and across the U.S., the takeaway is clear: if your network resembles a school system—centralized, resource-constrained, and user-heavy—you are already a target.
What Happened: A Quick Breakdown of the C2k Cyber Attack Northern Ireland
The C2k cyber attack Northern Ireland incident impacted a centralized IT network used by the majority of schools under the Education Authority Northern Ireland (EA NI).
Key disruptions included:
- Email systems going offline
- Student and staff login issues
- Administrative access restrictions
- Forced password reset advisory across schools
What made this particularly severe was timing—it occurred during critical exam preparation periods, amplifying operational disruption.
While the full root cause is still under investigation, early indicators suggest:
- Possible unauthorized access or ransomware activity
- Network-wide precautionary lockdown measures
👉 Unlike typical outages, this wasn’t just technical—it directly affected education continuity.
⚠️ Impact on Schools: Why This Was More Than Just Downtime
This wasn’t a simple IT outage—it exposed systemic vulnerabilities.
Immediate Consequences:
- Exam preparation delays impacting thousands of students
- Communication breakdown between teachers, students, and administrators
- Loss of access to learning platforms and internal systems
Hidden Risks:
- Potential student data breach exposure
- Compromised staff credentials
- Increased phishing vulnerability post-incident
The Bigger Problem:
Most schools rely on centralized IT infrastructure (like C2k). When that fails:
One breach can affect hundreds of institutions simultaneously.
For SMBs in North Carolina, this is a familiar pattern—shared cloud platforms, MSP dependencies, and limited in-house IT create identical risk profiles.
How the Attack Likely Happened (Based on Proven Cyberattack Frameworks)
While official confirmation is pending, cyber incidents like this typically follow predictable patterns.
Common Entry Points:
- Phishing-Based Credential Compromise
Attackers trick users into revealing login credentials through fake emails.
👉 Schools are especially vulnerable due to:
- High email volume
- Low cybersecurity awareness among users
- Weak Password Policies
If systems lack:
- Password complexity requirements
- Rotation policies
Attackers can easily exploit reused credentials.
- Lack of Multi-Factor Authentication (MFA)
Without MFA:
A single stolen password = full network access
- Unpatched Systems
Outdated software provides known vulnerabilities attackers can exploit in minutes.
- Third-Party Network Dependency (C2k Risk)
The C2k network acts as a centralized provider.
👉 This creates:
- A single point of failure
- A high-value target for attackers
🛡️ 5-Step Cybersecurity Framework to Prevent School & SMB Ransomware Attacks
This is where most blogs fail—they stop at “awareness.”
Let’s fix that.
✅ Step 1: Enforce Multi-Factor Authentication (MFA)
- Protects against 90%+ of credential-based attacks
- Apply to:
- VPN
- Cloud systems
✅ Step 2: Implement Zero Trust Architecture
Never trust—always verify.
- Limit lateral movement inside networks
- Segment access by role
👉 Reduces breach impact by 60–80%
✅ Step 3: Run Phishing Simulations & Training
Human error is the #1 attack vector.
- Quarterly training reduces risk significantly
- Simulations improve detection rates
✅ Step 4: Follow the 3-2-1 Backup Rule
- 3 copies of data
- 2 different storage types
- 1 offsite
👉 Ensures recovery even after ransomware encryption
✅ Step 5: Deploy 24/7 Monitoring & Incident Response
- Detect threats in <5 minutes
- Respond before widespread damage
👉 This is where managed IT services for education security become critical.
What Should Schools Do After a Cyberattack?
If you take one section seriously—make it this one.
Immediate Response Checklist:
- Isolate the Network
- Disconnect affected systems
- Prevent spread
- Force Password Resets
(Exactly what happened in the C2k incident)
- Identify the Entry Point
- Audit logs
- Check admin accounts
- Communicate Transparently
- Inform staff, students, parents
- Avoid panic, provide clarity
- Address Legal & Compliance
- GDPR requirements (for UK/EU)
- Data breach notification timelines
📊 Lessons from the Northern Ireland School Cyberattack
- Centralized Systems = High Risk
Convenience comes with vulnerability.
- Schools Are Prime Targets
Why?
- Limited budgets
- Weak defenses
- High data value
- Reactive IT Is No Longer Enough
By the time you detect a breach:
Damage is already done.
- Cybersecurity Maturity Gap Is Growing
Education sector lags behind finance and healthcare.
💼 Why SMBs in Raleigh, Durham & Cary Should Pay Attention
This isn’t just a UK problem.
SMBs share the same vulnerabilities:
- Limited IT staff
- Heavy reliance on cloud systems
- Weak endpoint security
Real Example:
A 50-employee business in Raleigh using:
- Microsoft 365
- Shared login practices
- No MFA
👉 This setup is nearly identical to vulnerable school networks
How MSPs Help Prevent Incidents Like the C2k Cyber Attack
Managed Service Providers (MSPs) fill the gap most organizations can’t handle internally.
Key Services:
- Managed Detection & Response (MDR)
- Security audits & vulnerability assessments
- Compliance (HIPAA, GDPR, etc.)
- Employee cybersecurity training
Real Outcome Example:
A mid-sized organization implementing MSP-led security:
- Reduced phishing success rate by 75%
- Detected threats 3x faster
- Achieved full compliance within 90 days
FAQs
What happened in the Northern Ireland school cyberattack?
A cyberattack on the C2k network disrupted IT systems across multiple schools, forcing password resets and limiting access during exam preparation.
How did the C2k network get hacked?
While unconfirmed, likely causes include phishing, weak credentials, lack of MFA, or third-party vulnerabilities.
What systems were affected?
Email, login systems, administrative access, and learning platforms.
How can schools prevent cyber attacks like C2k?
By implementing MFA, zero trust architecture, employee training, backups, and continuous monitoring.
What should organizations do after a cyberattack?
Isolate systems, reset credentials, investigate the breach, communicate clearly, and meet compliance requirements.

