Washington Hotel Chain Hit by Ransomware: What North Carolina Businesses Should Learn from the Japan Cyberattack
Cyberattacks no longer make headlines only when banks or technology giants are targeted. Increasingly, global hospitality brands are finding themselves in the crosshairs of sophisticated threat actors. The recent Washington Hotel ransomware attack in Japan is a clear reminder that no industry is immune—and for business leaders in North Carolina, the implications are closer to home than they may appear.
While the incident occurred overseas, the ripple effects of a Japanese hotel ransomware attack extend far beyond Japan’s borders. The hospitality industry operates on interconnected reservation systems, third-party vendors, and global payment networks. When a major brand like Washington Hotel—operated under WHG Hotels and owned by Fujita Kanko Inc.—is affected, it becomes a case study in modern cyber risk.
In this comprehensive analysis, we’ll examine what happened, how it happened, what was impacted, and—most importantly—what organizations in North Carolina can learn from this evolving hospitality industry ransomware breach.
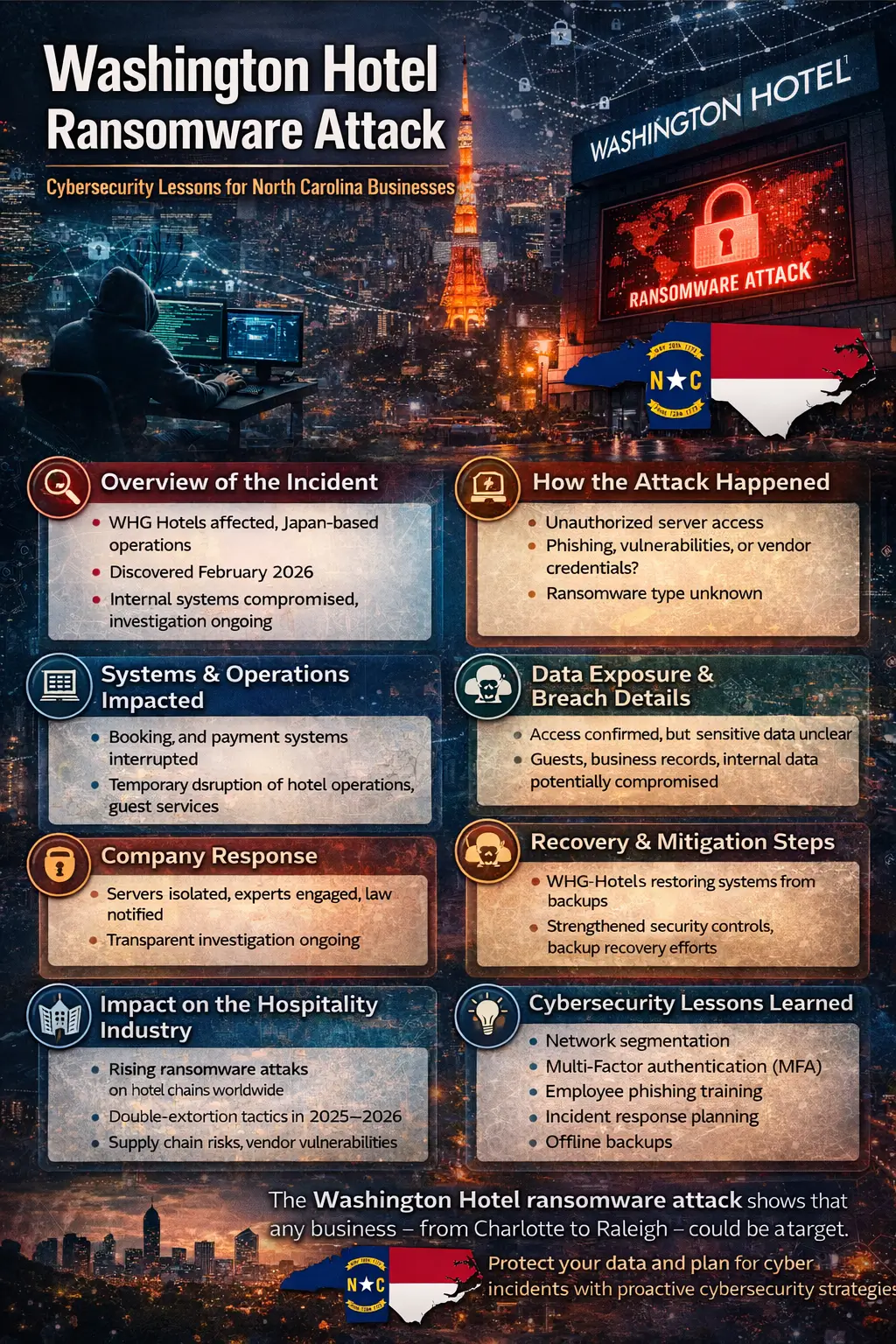
Overview of the Incident: What Happened?
The Washington Hotel Japan ransomware incident was disclosed in February 2026 after the company identified suspicious activity within its internal systems. The entity affected was WHG Hotels, which operates the Washington Hotel brand across Japan. The parent company, Fujita Kanko Inc., acknowledged the cybersecurity event publicly.
What Happened?
- Unauthorized access was confirmed on hotel servers.
- Internal business systems were disrupted.
- Operations experienced temporary instability.
- An investigation was launched immediately.
This WHG Hotels ransomware incident primarily affected Japan-based operations. While the brand name “Washington Hotel” may sound American, it is a well-established Japanese hospitality chain with a strong domestic footprint.
Initial Disclosure Details
The company reported that certain internal systems had been compromised, prompting containment measures. At the time of disclosure, officials stated that investigations were ongoing and that they were working with cybersecurity specialists to assess the extent of the impact.
In simple terms:
- Who was affected? WHG Hotels (Washington Hotel brand) under Fujita Kanko Inc.
- Where? Japan
- When? Discovered and disclosed in February 2026
- What? A ransomware attack that disrupted internal systems
How the Attack Happened (What We Know So Far)
In many ransomware cases, the technical details unfold gradually. In this instance, unauthorized server access ransomware activity was confirmed, indicating that attackers infiltrated internal infrastructure.
While the precise entry point has not been officially confirmed, common vectors in similar attacks include:
- Phishing emails targeting employees
- Exploitation of unpatched vulnerabilities
- Compromised remote access credentials
- Third-party vendor infiltration
Whether this attack involved phishing or exploitation of a vulnerable system remains under investigation. What is clear is that servers were compromised by ransomware, leading to system encryption and operational disruption.
Was Data Encrypted, Exfiltrated, or Both?
Modern ransomware groups increasingly deploy “double-extortion” tactics:
- Encrypt data.
- Steal sensitive information.
- Threaten public release if ransom is not paid.
At the time of reporting, the company indicated that investigations were ongoing regarding data exposure. It has not publicly confirmed whether customer data was accessed.
Systems & Operations Impacted
When ransomware hits a hotel chain, the consequences are not abstract—they affect real people in real time.
In this case, the ransomware attack disrupted hotel operations across affected properties in Japan.
Reported Impacts Included:
- Temporary disruption to hotel systems
- Booking system interruptions
- Credit card terminal outage hotel scenarios
- Internal business systems instability
- Service delays for guests
Imagine checking into a hotel after a 14-hour flight only to find that the reservation system is down. That’s the operational reality when ransomware impacts Japan hotel operations.
What About Loyalty Programs?
Reports indicated that loyalty platforms such as Washington Net were not significantly impacted. In fact, early communication suggested Washington Net loyalty data unaffected, though ongoing reviews continue.
For hospitality brands, operational downtime is often more damaging in the short term than the ransom demand itself. Hotels operate 24/7. Even a few hours of disruption can create cascading effects.
Data Exposure & Breach Details
A central concern in any Washington Hotel data breach is whether guest data was compromised.
At the time of reporting:
- The company confirmed unauthorized access.
- Investigations are ongoing ransomware breach assessments.
- It has not confirmed whether customer data was accessed.
Potentially Compromised Data Could Include:
- Guest names and contact information
- Reservation history
- Business records
- Internal documents
- Vendor communications
However, it is important to state clearly:
The company has not confirmed whether customer data was accessed.
Until forensic investigations are complete, the full scope of the WHG Hotels JP data breach remains under evaluation.
Company Response
The response to a cyber incident often determines long-term reputational impact.
Immediate Containment Measures
- Isolation of affected systems
- Network segmentation
- Server shutdown to prevent further spread
Engagement of Experts
The company engaged external cybersecurity professionals to conduct forensic investigations and support remediation.
Law Enforcement Involvement
As with most significant ransomware events, authorities were notified.
Public Communication
Fujita Kanko issued public statements acknowledging the incident. Transparent disclosure is increasingly expected in today’s regulatory environment.
Effective Washington Hotel breach response and recovery measures are critical to restoring trust.
Recovery & Mitigation Steps
Recovery in ransomware cases is rarely instantaneous.
Key recovery steps typically include:
- System restoration from backups
- Infrastructure scanning for persistent threats
- Credential resets
- Enhanced monitoring
Although the full restoration timeline has not been disclosed, organizations typically require days or weeks to return to complete operational normalcy after such events.
The incident also provides an opportunity for strengthened security controls, including improved endpoint detection, patch management, and authentication protocols.
Impact on the Hospitality Industry
The hospitality industry cyber threat landscape has evolved dramatically in recent years.
Hotels are attractive targets because they:
- Process large volumes of payment data
- Store personal guest information
- Operate centralized reservation systems
- Depend on uninterrupted service
A ransomware attack disrupts hotel operations in a way that directly affects customer experience.
Comparison to Past Incidents
Other global hotel brands have faced ransomware or data breaches in recent years. This pattern demonstrates a growing trend of hospitality-focused cybercrime.
For North Carolina hotel operators—from Charlotte to Raleigh—this incident is not distant news. It is a warning.
Broader Cybersecurity Trends (2025–2026)
The growth of ransomware in 2025–2026 reflects several evolving tactics:
Double-Extortion Models
Attackers both encrypt and exfiltrate data.
Supply Chain Risks
Hotels rely heavily on:
- Reservation software vendors
- Payment processors
- Cloud service providers
A vulnerability in any partner can expose the entire organization.
Third-Party Vendor Vulnerabilities
The interconnected nature of modern IT infrastructure means that a breach at one point can cascade.
The ransomware hotel brand Fujita Kanko Inc. case underscores these realities.
Cybersecurity Lessons Learned
For North Carolina businesses—especially those in hospitality, healthcare, and retail—there are clear lessons.
- Network Segmentation
Isolate critical systems to prevent lateral movement.
- Multi-Factor Authentication (MFA)
MFA dramatically reduces unauthorized access risks.
- Regular Vulnerability Patching
Unpatched systems remain a top entry point for attackers.
- Employee Phishing Training
Human error remains one of the biggest vulnerabilities.
- Incident Response Planning
Have a tested, documented plan before an attack occurs.
- Offline Backups
Backups must be isolated to prevent encryption by ransomware.
These cybersecurity lessons from hotel ransomware incidents apply equally to businesses in Raleigh, Durham, and across North Carolina.
Regulatory & Legal Considerations
Japan enforces data protection regulations that require breach notification and transparency. If customer data were confirmed exposed, regulatory scrutiny would follow.
For U.S.-based businesses, similar frameworks include:
- State data breach notification laws
- Federal sector-specific regulations
- PCI DSS requirements for payment systems
Potential consequences include:
- Regulatory fines
- Civil litigation
- Reputational damage
The legal exposure associated with a confirmed Washington Hotel data breach would depend on the scope of compromised data.
What Hotel Guests Should Do
If guest data is later confirmed to have been accessed, customers should:
- Monitor financial accounts
- Watch for phishing emails
- Change passwords associated with hotel accounts
- Enable credit monitoring services
Even when confirmation is pending, vigilance is wise.
Ongoing Investigation & Future Updates
At the time of publication:
- Investigation ongoing ransomware breach reviews continue.
- No confirmed ransom payment has been publicly disclosed.
- Full restoration timelines have not been finalized.
As forensic analysis progresses, additional updates may clarify the scope of impact.
Final Thoughts for North Carolina Business Leaders
The Washington Hotel Japan ransomware event is more than an overseas news story. It is a case study in modern cyber risk management.
If a well-established hotel brand under Fujita Kanko can experience a ransomware incident affecting business systems, any organization can.
For North Carolina businesses—whether you operate a boutique hotel in Asheville, a medical practice in Cary, or a law firm in Durham—the message is clear:
Cybersecurity is not an IT issue.
It is a business continuity issue.
It is a brand trust issue.
And increasingly, it is a survival issue.
The question is no longer whether ransomware will target your industry. The question is whether you are prepared when it does.
Frequently Asked Questions (FAQs) Washington Hotel Ransomware Attack
- What happened in the Washington Hotel ransomware attack?
The Washington Hotel ransomware attack involved unauthorized access to internal servers operated by WHG Hotels in Japan, a subsidiary of Fujita Kanko Inc. The cybersecurity incident was discovered in February 2026 and resulted in temporary disruption to hotel systems. An investigation is ongoing to determine the full scope of the breach.
- Was customer data exposed in the Washington Hotel data breach?
At the time of reporting, the company confirmed unauthorized access to internal systems but has not confirmed whether customer data was accessed. Investigators are reviewing whether guest information, business records, or internal documents were compromised as part of the WHG Hotels JP data breach.
- How did the ransomware attack happen?
While technical details have not been fully disclosed, the attack involved unauthorized server access. Possible entry points in similar incidents include phishing emails, compromised credentials, unpatched vulnerabilities, or third-party vendor exposure. The investigation into the exact cause remains ongoing.
- Were hotel operations disrupted?
Yes. The ransomware attack disrupted hotel operations in Japan. Reports indicate temporary booking system interruptions, internal system instability, and possible credit card terminal outages at certain properties. However, core services were gradually restored as containment measures were implemented.
- Was the Washington Net loyalty program affected?
Early communications suggested that Washington Net loyalty data was unaffected. However, the company continues to assess systems as part of its broader data breach response and investigation.
- What is WHG Hotels and Fujita Kanko’s role in this incident?
WHG Hotels operates the Washington Hotel brand in Japan. Fujita Kanko Inc. is the parent company. Both entities are involved in managing the response to the ransomware hotel brand Fujita Kanko Inc. cybersecurity incident, including engaging experts and coordinating recovery efforts.
- Did the company pay the ransom?
As of the latest updates, there has been no public confirmation regarding ransom payment. In many ransomware cases, organizations do not disclose payment details due to legal, investigative, or security reasons.
- Why are hotels targeted in ransomware attacks?
The hospitality industry is considered a high-value target because hotels:
- Store large volumes of guest personal data
- Process payment card information
- Rely on centralized reservation systems
- Operate 24/7 with limited downtime tolerance
A ransomware attack disrupts hotel operations quickly, increasing pressure on organizations to restore systems.
- How does this Japanese hotel ransomware attack affect North Carolina businesses?
Although the Washington Hotel Japan ransomware incident occurred overseas, it highlights vulnerabilities that exist globally. North Carolina businesses—especially hotels, healthcare providers, law firms, and retail organizations—face similar risks involving unauthorized server access, phishing attacks, and third-party vendor exposure.
The incident serves as a warning that proactive cybersecurity measures are essential regardless of geography.
- What cybersecurity lessons can businesses learn from this attack?
Key lessons from this hospitality industry ransomware breach include:
- Implement multi-factor authentication (MFA)
- Maintain regular vulnerability patching
- Segment networks to limit lateral movement
- Conduct employee phishing awareness training
- Maintain secure, offline backups
- Develop and test an incident response plan
Preparedness significantly reduces the impact of ransomware incidents.
- What should hotel guests do if their data may have been exposed?
If customer data is later confirmed to have been accessed, guests should:
- Monitor financial accounts for unusual activity
- Watch for phishing emails referencing hotel stays
- Change passwords linked to hotel accounts
- Consider enabling credit monitoring services
Even in the absence of confirmed exposure, vigilance is recommended.
- Is ransomware becoming more common in 2025–2026?
Yes. Ransomware attacks continue to increase globally. Threat actors are increasingly using double-extortion tactics—encrypting data and threatening public release. Supply chain risks and third-party vendor vulnerabilities have also contributed to the growing threat landscape.
- What is the current status of the investigation?
The investigation into the Washington Hotel ransomware attack remains ongoing. Cybersecurity experts are conducting forensic analysis to determine the scope of system compromise, potential data exposure, and root cause. Additional updates are expected as the review progresses.
- Could a similar ransomware attack happen to businesses in Raleigh, Durham, or Charlotte?
Yes. Ransomware does not target organizations based on geography—it targets vulnerabilities. Any business in North Carolina that relies on digital infrastructure, payment processing systems, or cloud-based platforms could face similar risks without adequate cybersecurity controls in place.

