Voice Phishing Attacks Are Rising: Lessons from the Aura Data Breach (2026 Case Study)
A cybersecurity company got hacked… using a phone call.
It sounds almost ironic. In an age of advanced firewalls, AI-driven threat detection, and zero-trust architectures, one of the most talked-about cybersecurity incidents of 2026—the Aura data breach—did not begin with malicious code or a sophisticated exploit. It began with a conversation.
This voice phishing attack, also known as a vishing attack, exposed nearly 900,000 records and once again proved a hard truth:
👉 Hackers don’t hack systems—they hack people.
For small and medium-sized businesses across Raleigh, Durham, Cary, and broader North Carolina, this incident is more than just news. It is a warning.
Let’s unpack what really happened, how ShinyHunters executed this social engineering attack, and most importantly—what your business can learn before it’s too late.
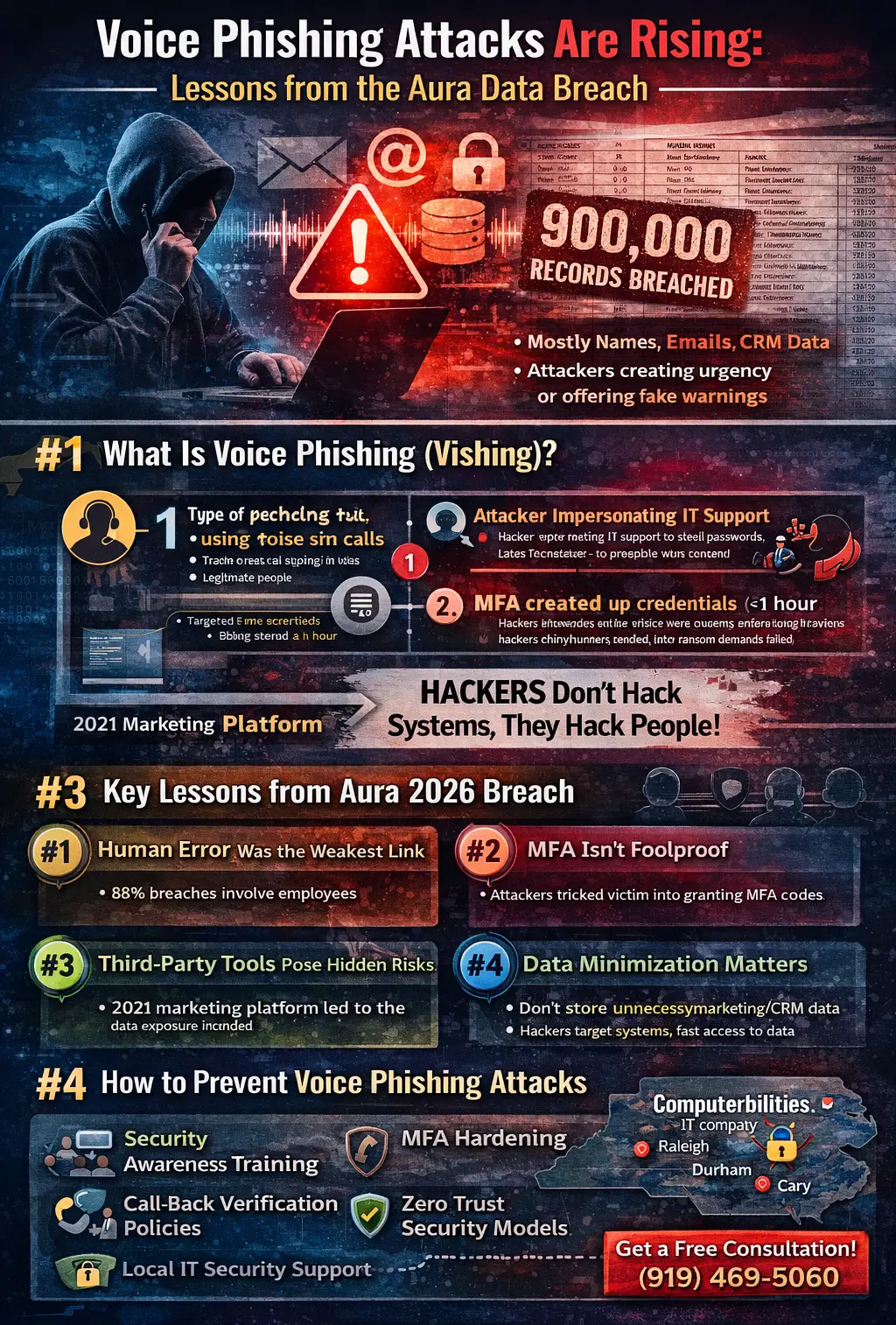
What Is Voice Phishing (Vishing)?
Before diving into the Aura data breach 2026, it’s important to understand the core attack method.
Definition
Voice phishing (vishing) is a type of social engineering attack where cybercriminals use phone calls to trick individuals into revealing sensitive information such as login credentials, MFA codes, or internal system access.
How It Differs from Traditional Phishing
Most businesses are familiar with email phishing. But vishing operates differently:
Email Phishing | Voice Phishing (Vishing) |
Relies on suspicious emails | Relies on real-time phone calls |
Can be filtered by tools | Harder to detect automatically |
Gives user time to think | Creates urgency and pressure |
Often generic | Highly personalized |
Real-World Example
Imagine receiving a call from someone claiming to be from your IT department:
“We’ve detected suspicious activity on your account. I need to verify your login and send you a code to secure your system.”
It sounds legitimate. It feels urgent. And that’s exactly the point.
What Happened in the Aura Data Breach?
The Aura data breach stands as one of the most important data breach case studies of 2026.
Key Facts:
- Attack Type: Voice phishing (vishing attack)
- Threat Actor: ShinyHunters
- Records Exposed: ~900,000
- Data Type: Names, emails, marketing/CRM data
- Access Time: Approximately 1 hour
- Source: Legacy marketing database
The Entry Point: Human Error
The attack began when an employee was targeted through a vishing call. There was no malware, no brute-force attack, and no system vulnerability exploited.
👉 The attacker simply convinced the employee to provide access.
This is what makes this voice phishing data breach so significant. It bypassed every traditional cybersecurity layer.
How the Attack Actually Worked
To truly understand the risk, let’s break down how hackers use vishing to steal data.
Step-by-Step Breakdown
- Impersonation
The attacker posed as a legitimate internal or support entity—likely IT or a service provider.
- Establishing Trust
Using professional language and urgency, they created a believable scenario:
- “Security issue detected”
- “Immediate action required”
- Credential Extraction
The employee was tricked into sharing:
- Login credentials
- MFA codes
- System access information
- System Access
Within less than an hour, attackers gained access to internal systems—specifically a marketing/CRM database.
- Data Exfiltration
- ~900,000 records extracted
- Approx. 12GB of data stolen
- Ransom & Leak
- ShinyHunters demanded ransom
- When negotiations failed, data was leaked
Why This Attack Was So Dangerous
At first glance, some might dismiss this breach because it did not involve financial data or passwords. That would be a mistake.
- It Bypassed Technical Defenses
Firewalls, antivirus, and endpoint detection tools were irrelevant because:
👉 The attacker was granted access
- It Exploited Human Psychology
The success of the attack depended on:
- Trust
- Urgency
- Authority
- It Was Fast
The breach occurred in under an hour, leaving little time for detection.
- It Was Scalable
This same method can be used across:
- Multiple employees
- Multiple companies
- Multiple industries
Key Lessons from the Aura Breach
This ShinyHunters data breach offers several critical lessons for businesses.
🔑 Lesson 1: Humans Are the Weakest Link
Even the most secure systems can fail if employees are not trained.
🔑 Lesson 2: MFA Is Not Foolproof
Attackers can:
- Trick users into sharing MFA codes
- Use real-time interception
🔑 Lesson 3: Third-Party Tools Are Risky
The compromised data came from a legacy marketing platform.
👉 Old systems = hidden vulnerabilities
🔑 Lesson 4: Data Minimization Matters
Why was outdated data still accessible?
Businesses must:
- Delete unused data
- Limit access to sensitive systems
🔑 Lesson 5: Attackers Prefer Social Engineering
It’s easier to manipulate a person than break encryption.
Why Voice Phishing Attacks Are Rising in 2026
The rise of vishing attacks is not accidental—it’s strategic.
- AI Voice Cloning
Attackers can now mimic:
- Executives
- IT staff
- Vendors
- Remote Work Culture
Employees are:
- Less connected to internal teams
- More reliant on phone/email communication
- Helpdesk Impersonation Attacks
IT support is a trusted authority—making it a perfect disguise.
- Ransomware + Social Engineering
Modern attacks combine:
- Data theft
- Extortion
- Social engineering
How Businesses Can Prevent Voice Phishing Attacks
For SMBs in North Carolina, prevention is not optional—it’s essential.
- Security Awareness Training
Train employees to:
- Recognize suspicious calls
- Never share credentials over phone
- Call-Back Verification Policies
Implement a simple rule:
👉 “Never trust inbound requests—verify through official channels”
- Zero Trust Access
Limit access based on:
- Role
- Context
- Device
- MFA Hardening
Use:
- App-based authentication
- Hardware tokens
Avoid:
- SMS-based MFA
- Identity & Endpoint Monitoring
Monitor:
- Login anomalies
- Data access patterns
What Businesses in North Carolina Should Take Seriously
If you operate in Raleigh, Cary, or Durham, you are not immune.
In fact, SMBs are often:
- Easier targets
- Less protected
- More likely to pay ransom
Common Risk Areas:
- Small IT teams
- Lack of employee training
- Legacy systems
- Overexposed data
What Individuals Should Do If Affected
If you suspect involvement in a voice phishing data breach:
- Monitor your accounts
- Watch for phishing emails
- Enable strong MFA
- Use identity protection tools
- Report suspicious activity immediately
How Computerbilities Helps Protect Your Business
At Computerbilities, we specialize in helping businesses across North Carolina stay ahead of evolving cyber threats.
Our Services Include:
- Managed IT services cybersecurity
- Phishing protection and simulation training
- 24/7 threat monitoring
- Identity and access management
- Endpoint security solutions
We don’t just install security tools—we build resilient organizations.
FAQs
- What is a voice phishing attack?
A voice phishing (vishing) attack is a social engineering attack where scammers use phone calls to trick individuals into revealing sensitive information.
- How did the Aura data breach happen?
The breach occurred when an employee was deceived through a vishing call, giving attackers access to a marketing database containing ~900,000 records.
- What data was exposed in the Aura breach?
Names, email addresses, and marketing/CRM data were exposed—making victims more vulnerable to future phishing attacks.
- Why are vishing attacks increasing?
Due to AI voice cloning, remote work, and the effectiveness of social engineering tactics.
- How can businesses prevent voice phishing attacks?
Through employee training, verification protocols, MFA security, and managed cybersecurity services.
- Are small businesses at risk?
Yes—SMBs are often primary targets due to limited cybersecurity resources.
Final Thoughts
The Aura data breach 2026 is not just another cybersecurity headline. It is a reminder that the battlefield has shifted.
The most advanced threat today is not a piece of malware—it’s a conversation.
For businesses across North Carolina, the message is clear:
👉 Technology alone is not enough.
👉 Awareness is your first line of defense.
Because in the era of voice phishing attacks, the question is no longer if your business will be targeted—but when.