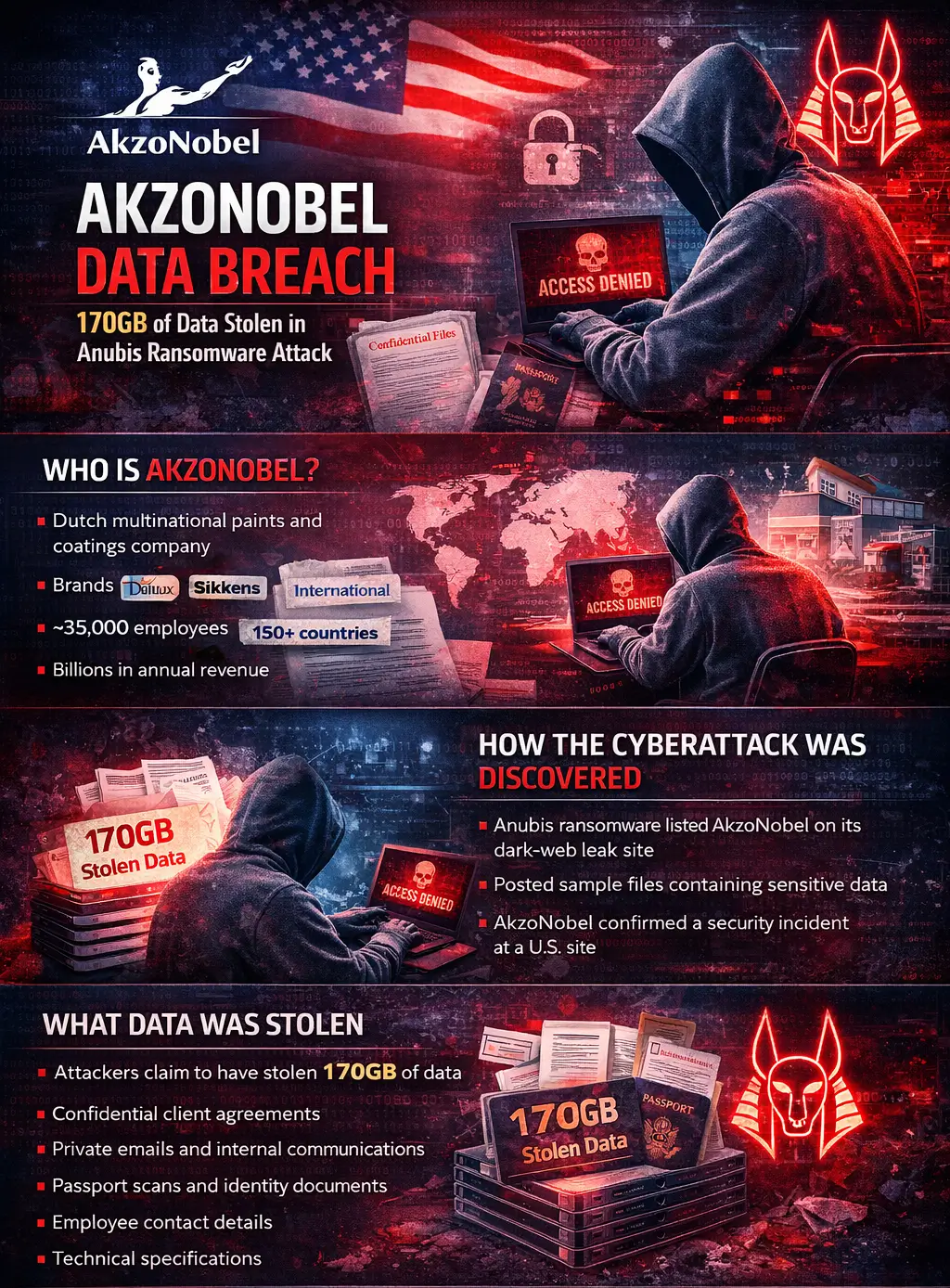
AkzoNobel Data Breach – 170GB of Data Stolen in Anubis Ransomware Attack
Introduction: A Cyberattack on One of the World’s Largest Paint Manufacturers
Cyberattacks are no longer limited to tech companies or financial institutions. Increasingly, they are targeting industrial giants that form the backbone of global supply chains. One of the latest examples is the AkzoNobel data breach, which has raised serious concerns across the cybersecurity community.
In early March 2026, AkzoNobel confirmed that hackers breached the network of one of its United States facilities. The attack was allegedly carried out by the Anubis ransomware group, which claims to have stolen 170GB of sensitive corporate data.
Although the company stated the AkzoNobel cyberattack was contained and limited to a single site, the attackers claim to possess roughly 170,000 files containing confidential information, including internal emails, passport scans, and technical documents.
For businesses across North Carolina and the United States, this incident serves as another reminder that industrial cybersecurity threats are rapidly evolving.
Who Is AkzoNobel?
To understand why this breach matters, it helps to know the scale of the organization involved.
AkzoNobel is a Dutch multinational paints and coatings company headquartered in Amsterdam. The company is one of the largest manufacturers of decorative paints and industrial coatings in the world.
Its portfolio includes well-known global brands such as:
- Dulux
- Sikkens
- International
- Interpon
These products are used across industries ranging from construction and automotive manufacturing to aerospace and marine engineering.
The company employs over 35,000 people and operates in more than 150 countries, generating billions in annual revenue.
This scale makes the AkzoNobel network breach particularly significant. When organizations of this size experience cyber incidents, the consequences can ripple across global supply chains.
How the Cyberattack Was Discovered
The AkzoNobel ransomware incident first came to light not through the company itself, but through the tactics commonly used by ransomware gangs today.
The Anubis ransomware group listed AkzoNobel on its dark web leak site, claiming responsibility for the breach.
Ransomware groups often follow a predictable pattern:
- Break into a company’s network.
- Steal sensitive data.
- Encrypt systems.
- Threaten to publish the stolen information.
In the AkzoNobel case, the attackers allegedly skipped straight to the data exfiltration phase, claiming they had already stolen a large archive of company files.
To support their claims, the attackers published samples of the stolen data online, including screenshots and file listings.
Shortly afterward, AkzoNobel confirmed a security incident affecting one of its U.S. locations, stating that the attack had been contained and the impact was limited.
What Data Was Stolen in the AkzoNobel Breach?
According to claims made by the attackers, the breach involved a massive amount of information.
The Anubis ransomware gang alleges it stole approximately 170GB of data, consisting of nearly 170,000 files.
The leaked samples reportedly include:
- Confidential client agreements
- Private internal email communications
- Employee contact details
- Passport scans and identity documents
- Technical specifications and testing documents
- Internal corporate records
These types of files represent more than simple operational data. They can expose sensitive intellectual property and personally identifiable information.
For large manufacturers, technical documentation and material testing files can reveal proprietary formulas, research insights, and industrial processes.
In other words, the AkzoNobel data leak may not only impact individuals—it could potentially affect corporate competitiveness.
Who Is the Anubis Ransomware Group?
The group behind the attack is relatively new but rapidly gaining attention.
Anubis ransomware first appeared in late 2024 and operates using a Ransomware-as-a-Service (RaaS) model.
Under this model:
- Developers create the ransomware platform.
- Affiliates carry out attacks.
- Profits are shared between the two.
Reports indicate affiliates can receive up to 80% of ransom payments, making it an attractive option for cybercriminals.
Anubis is also known for aggressive tactics, including:
- Double extortion — encrypting files and stealing data
- Dark web leak sites — publishing stolen data to pressure victims
- Destructive file-wiping tools that permanently destroy encrypted files
This combination makes them particularly dangerous.
AkzoNobel’s Response to the Cyberattack
AkzoNobel responded to the incident with a relatively measured statement.
According to the company:
- The security incident occurred at one U.S. site
- The breach was contained quickly
- The overall impact was limited
The company also said it is:
- notifying affected parties
- working with authorities
- conducting a cybersecurity investigation
At this time, AkzoNobel has not confirmed whether it negotiated with the attackers or paid any ransom.
Why Manufacturing Companies Are Prime Targets
The AkzoNobel US site cyberattack is part of a broader trend.
Manufacturing companies are increasingly becoming top ransomware targets.
There are several reasons for this.
- Valuable Intellectual Property
Manufacturers often store proprietary formulas, engineering designs, and research data.
For cybercriminals, these files can be extremely valuable.
- Complex Supply Chains
A single manufacturing company can connect to hundreds of suppliers and partners.
Compromising one company can open doors to multiple downstream targets.
- Operational Pressure
If production lines stop due to a cyberattack, companies can lose millions of dollars per day.
That pressure makes them more likely to pay ransom demands.
- Legacy Systems
Industrial environments often run older software or specialized machinery that cannot be easily updated.
These systems create vulnerabilities that attackers can exploit.
Risks and Consequences of the Breach
Even if the AkzoNobel ransomware attack was contained quickly, several risks remain.
Identity Theft
Passport scans and personal documents could potentially be used for fraud.
Corporate Espionage
Technical documents and internal research could provide insights to competitors.
Supply Chain Exposure
If partner contracts and vendor data are exposed, other companies may also face risks.
Reputational Damage
Even a limited breach can damage trust among customers, suppliers, and investors.
Lessons Businesses Can Learn from the AkzoNobel Breach
For companies across North Carolina and the United States, the AkzoNobel incident offers several important lessons.
- Strengthen Endpoint Security
Every device connected to the network should be protected by modern endpoint detection tools.
- Monitor Networks Continuously
Cybercriminals often spend weeks inside a network before launching an attack.
Continuous monitoring can detect suspicious activity earlier.
- Patch Systems Regularly
Unpatched vulnerabilities remain one of the most common entry points for ransomware attacks.
- Train Employees
Many ransomware attacks begin with phishing emails.
Cybersecurity awareness training remains one of the most effective defenses.
- Prepare an Incident Response Plan
Organizations should have a clear plan for responding to cyber incidents.
The faster a breach is detected and contained, the lower the damage.
Conclusion: A Warning for Global Businesses
The AkzoNobel data breach demonstrates how even large multinational companies remain vulnerable to modern ransomware groups.
While the company says the breach was contained, the attackers claim to have stolen 170GB of sensitive information, highlighting the growing sophistication of cybercriminal operations.
For organizations everywhere—including businesses in North Carolina—the incident underscores a critical reality:
Cybersecurity is no longer optional.
Whether you are a global manufacturer or a regional business, the risks of ransomware, data leaks, and cyber extortion continue to rise.
Companies that invest in proactive cybersecurity, monitoring, and incident response planning will be far better positioned to withstand the next wave of cyber threats.
Frequently Asked Questions (FAQs) About the AkzoNobel Data Breach
- What happened in the AkzoNobel data breach?
The AkzoNobel data breach occurred after the Anubis ransomware group claimed it infiltrated the company’s network and stole approximately 170GB of data. The cyberattack reportedly affected a U.S. site operated by the global paints manufacturer. After the attackers posted evidence of stolen files on their dark-web leak site, AkzoNobel confirmed that a cybersecurity incident had occurred but said the breach was contained and its impact was limited. The company launched a cyber incident response investigation and began notifying relevant authorities and affected parties.
- How did the Anubis ransomware attack AkzoNobel?
According to cybersecurity reports, the Anubis ransomware attack on AkzoNobel likely followed the modern ransomware playbook. Attackers infiltrate a corporate network, quietly perform data exfiltration, and then threaten to publish stolen files unless a ransom is paid. In this case, the Anubis group listed AkzoNobel on its dark-web leak site and released sample files to prove they had access to sensitive information. This tactic is commonly known as double-extortion ransomware, where hackers steal data before encrypting systems.
- How much data was stolen in the AkzoNobel cyberattack?
The attackers claim that the AkzoNobel ransomware incident resulted in the theft of approximately 170GB of data, consisting of nearly 170,000 files. While AkzoNobel has not confirmed the exact volume of stolen data, cybersecurity analysts believe the breach may include internal corporate documents and sensitive employee information.
- What data was stolen in the AkzoNobel breach?
The AkzoNobel data leak allegedly includes a variety of sensitive corporate files. Sample data released by the attackers reportedly contained:
- Confidential client agreements
- Internal company emails and communications
- Passport scans and identity documents
- Employee contact information
- Technical specifications and testing reports
- Internal corporate documents
If confirmed, this type of sensitive data exposure could potentially create risks related to identity theft, corporate espionage, or supply chain vulnerabilities.
- Who is the Anubis ransomware group?
The Anubis ransomware group is a relatively new cybercriminal organization that emerged in late 2024. It operates under a Ransomware-as-a-Service (RaaS) model, where the creators of the malware provide tools and infrastructure to affiliates who conduct attacks. These affiliates often receive a large percentage of the ransom payments. The group is known for data exfiltration attacks and dark-web leak sites, where stolen files are published if victims refuse to pay.
- Was the AkzoNobel cyberattack contained?
Yes. According to company statements, the AkzoNobel US site cyberattack was contained, and the company reported that the impact was limited to a single facility. AkzoNobel stated that it is working with cybersecurity experts and law enforcement to investigate the incident and prevent further damage.
- Why are manufacturing companies targeted by ransomware attacks?
Manufacturing organizations like AkzoNobel are increasingly targeted because they store valuable intellectual property, industrial research data, and sensitive supply chain information. Additionally, manufacturing companies often operate with complex global networks and legacy systems, which can create vulnerabilities. Attackers also know that operational disruptions in manufacturing can be extremely costly, making companies more likely to pay ransom demands.
- What are the risks of a ransomware data leak like this?
A ransomware data leak can lead to several serious consequences, including:
- Identity theft if personal data is exposed
- Corporate espionage involving intellectual property
- Supply chain disruptions affecting partner companies
- Financial losses and regulatory penalties
- Reputational damage for the affected organization
Even if a company restores its systems, stolen data may still circulate on the dark web.
- How do companies respond to ransomware attacks?
When organizations experience a ransomware attack, they typically follow an incident response process that includes:
- Isolating affected systems
- Investigating the breach with cybersecurity experts
- Notifying regulators and affected individuals
- Restoring systems from secure backups
- Implementing stronger security controls to prevent future attacks
Many companies also conduct a full cyberattack investigation to identify how attackers gained access to their network.
- What lessons can businesses learn from the AkzoNobel breach?
The AkzoNobel network breach highlights several cybersecurity lessons for businesses:
- Implement strong endpoint protection and threat detection tools
- Maintain regular security patch updates
- Monitor networks for unusual activity
- Train employees to identify phishing and cyber threats
- Develop a comprehensive incident response plan
Organizations that invest in proactive industrial cybersecurity strategies are better prepared to defend against modern ransomware threats.

