Rituals Data Breach 2026: What Happened, What It Means, and Why Your Business Should Care
Even global luxury brands with millions of customers aren’t immune to cyberattacks.
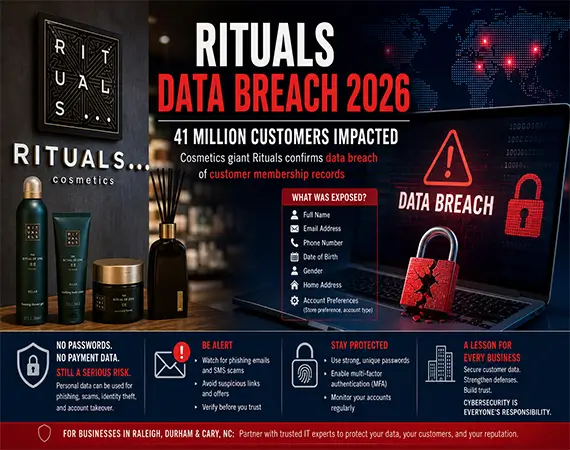
In April 2026, cosmetics giant Rituals confirmed a major data breach, exposing sensitive customer information from its “My Rituals” membership database. With over 40 million users globally, the incident quickly became one of the most talked-about cybersecurity events in the retail industry this year.
While no payment details or passwords were compromised, the breach raises a critical question:
👉 How dangerous is a data breach when financial data isn’t involved?
For businesses across Raleigh, Durham, Cary, and North Carolina, this incident serves as a powerful wake-up call.

What Happened in the Rituals Data Breach
The Rituals cybersecurity incident involved unauthorized access to its customer loyalty database—specifically the “My Rituals” membership system.
Attackers were able to:
- Gain unauthorized access
- Extract customer records
- Download sensitive personal information
This was not a ransomware attack or a payment system hack—it was something more subtle, yet equally concerning: data exfiltration of personal identifiable information (PII).
What Data Was Compromised
The Rituals customer data breach exposed:
- Full names
- Email addresses
- Phone numbers
- Dates of birth
- Gender
- Home/postal addresses
- Account preferences and membership details
⚠️ Important clarification:
- No passwords were leaked
- No financial/payment data was exposed
At first glance, this may seem like a “low-risk” breach.
But that assumption would be dangerously misleading.
How the Attack Occurred
While the exact technical details are still under investigation, early findings suggest:
- Unauthorized access to a backend database
- Possible exploitation of:
- Misconfigured systems
- API vulnerabilities
- Weak access controls
- Data was exfiltrated (downloaded) rather than encrypted
This type of attack is becoming increasingly common in eCommerce and loyalty platforms, where attackers focus on harvesting data quietly rather than disrupting operations.
Impact on Customers Worldwide
Rituals operates globally, and the breach affects:
- Europe
- United Kingdom
- Select users in the United States
With a user base exceeding 40 million members, even partial exposure represents a massive cybersecurity event.
However, the company has not disclosed the exact number of affected individuals.
Why This Breach Is More Dangerous Than It Seems
Here’s where things get serious.
Even without passwords or credit card details, this personal data exposure (PII leak) creates significant risk.
🎯 Targeted Phishing Attacks
Attackers now have:
- Real names
- Contact details
- Demographic information
This allows them to craft highly convincing phishing emails, such as:
- “Exclusive birthday rewards”
- “Membership renewal notices”
- “Account verification alerts”
🧠 Social Engineering Risks
With enough personal data, attackers can:
- Impersonate customer service
- Trick users into revealing passwords
- Gain access to other accounts
🔐 Identity Theft Potential
While limited, combining this data with other leaks can:
- Enable identity profiling
- Increase fraud success rates
👉 Key takeaway:
Low-risk breaches can still be high-impact.
Rituals’ Response and Investigation
To its credit, Rituals acted quickly:
- Contained the breach
- Notified affected customers
- Reported the incident to authorities
- Initiated a forensic cybersecurity investigation
- Began monitoring for dark web exposure
This aligns with GDPR compliance requirements, especially for European users.
Rising Threat to Loyalty Programs
This incident highlights a growing trend:
👉 Customer loyalty programs are prime targets for hackers.
Why?
Because they contain:
- Rich personal data
- Behavioral insights
- Contact information
Unlike payment systems, these databases often have:
- Weaker security controls
- Broader internal access
Recent breaches in companies like Marks & Spencer and Co-op show a clear pattern.
Risks for Customers
Customers affected by the My Rituals membership breach should watch for:
📧 Phishing Emails
Messages that appear legitimate but contain malicious links
📱 SMS Scams
Text messages offering fake promotions
🎁 Fake Offers
“Exclusive deals” designed to trick users
📉 Increased Spam
Data may be sold or shared on underground markets
How to Stay Safe After a Data Breach
Here are practical steps every user should take:
- Be Skeptical of Emails
Never click links from unknown or suspicious sources
- Use Strong Passwords
Even if not exposed, update passwords regularly
- Enable Multi-Factor Authentication (MFA)
Adds an extra layer of protection
- Monitor Your Accounts
Watch for unusual activity
- Avoid Sharing Personal Information
Especially over email or phone
What Businesses in North Carolina Must Learn
For small and medium businesses in Raleigh, Durham, and Cary, this breach offers critical lessons.
🔒 Secure Customer Databases
Implement encryption and strict access controls
🧱 Adopt Zero Trust Architecture
Never assume internal systems are safe
🔍 Conduct Regular Security Audits
Identify vulnerabilities before attackers do
👨💻 Train Employees
Human error remains a top cause of breaches
🛡️ Partner with IT Security Experts
Managed IT services can provide:
- 24/7 monitoring
- Threat detection
- Incident response
Real-World Example
Think of your customer database like a VIP guest list at a private event.
Even if no money is stolen, if that list gets leaked:
- Guests can be targeted
- Fake invitations can be sent
- Trust is compromised
That’s exactly what happened here.
Conclusion
The Rituals data breach 2026 is a powerful reminder that cybersecurity isn’t just about protecting money—it’s about protecting trust.
For businesses, especially in North Carolina, the message is clear:
👉 If global brands can be breached, so can you.
The difference lies in preparation, prevention, and response.
FAQs
What data was stolen in the Rituals breach?
Personal data such as names, emails, phone numbers, and addresses.
Is the Rituals data breach dangerous?
Yes, due to phishing and social engineering risks.
Were passwords or payment details leaked?
No, those were not compromised.
How can customers protect themselves?
Enable MFA, avoid suspicious emails, and monitor accounts.
Why are loyalty programs targeted?
They contain valuable personal and behavioral data.