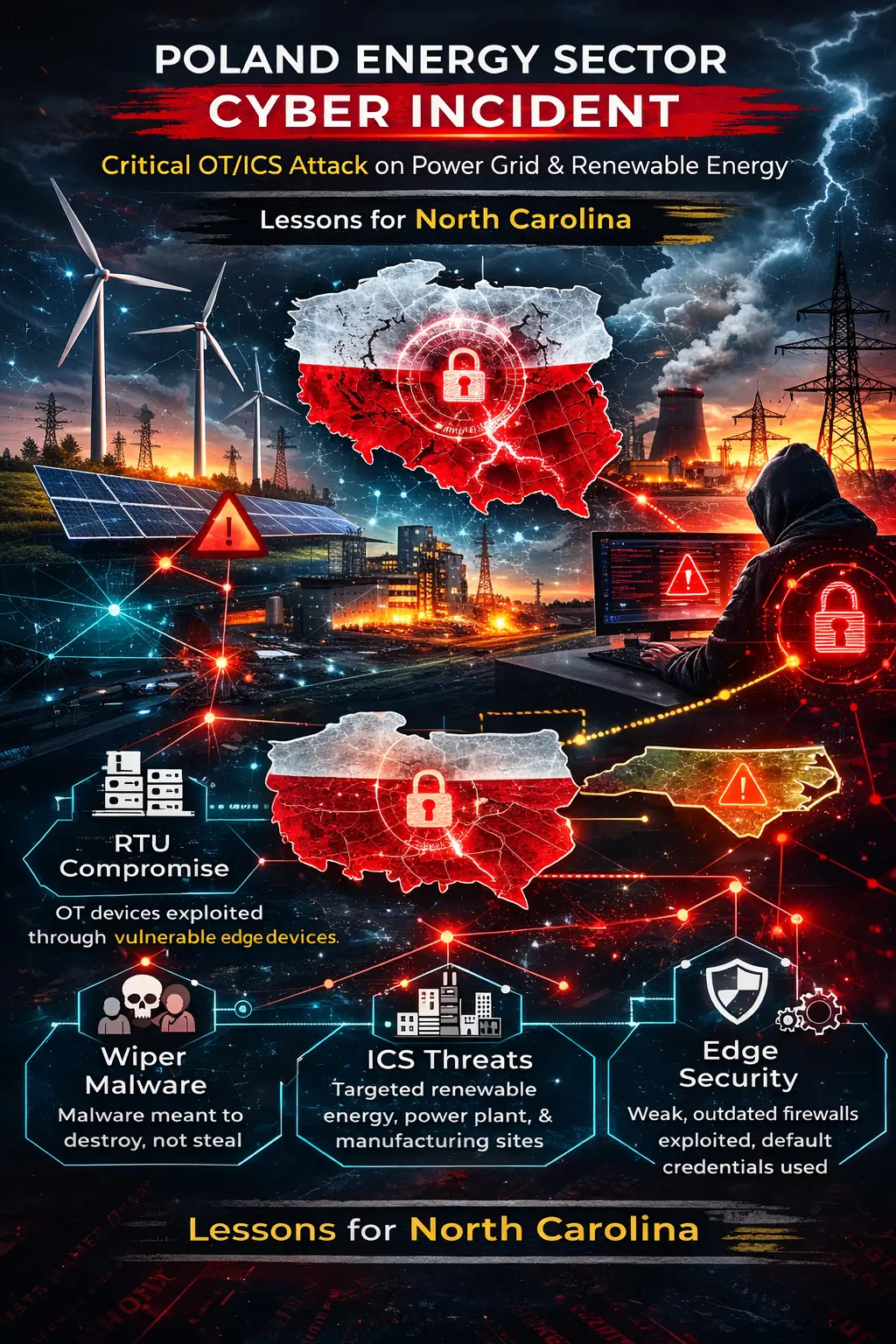
Poland Energy Sector Cyber Incident: What North Carolina Energy Leaders Must Learn from a Coordinated OT/ICS Cyber Attack
Critical infrastructure attacks no longer make headlines simply because they occur. They make headlines because of what they reveal.
The Poland energy sector cyber incident that unfolded on December 29, 2025, was not a ransomware stunt. It was not a data breach designed for extortion. It was something far more strategic — a coordinated, destructive operational technology (OT) attack targeting renewable energy facilities and power infrastructure.
For organizations in North Carolina, where energy innovation, renewable expansion, and distributed grid modernization are accelerating, this incident offers important lessons. Whether you operate wind farms, solar arrays, municipal utilities, manufacturing facilities, or industrial systems connected to energy distribution, the Poland energy sector cyber attack provides a real-world case study in OT/ICS cybersecurity gaps.
This article breaks down what happened, how it happened, why it matters, and what North Carolina organizations should be doing now.
Incident Overview: December 29, 2025
On December 29, 2025, a coordinated cyberattack targeted Poland’s energy infrastructure. Unlike opportunistic cybercrime, this was deliberate and destructive.
Targeted Systems Included:
- 30+ wind and photovoltaic farms
- A large combined heat and power (CHP) plant
- A manufacturing sector company
This was not a ransomware campaign. There were no public ransom demands. Instead, attackers deployed destructive tooling designed to interfere with operational technology systems.
The event has been widely described as a:
- Poland power grid cyberattack
- Poland renewable energy cyberattack
- OT/ICS cybersecurity incident Poland
- Poland critical infrastructure cyber incident
The distinctive element? It focused on operational technology (OT) and industrial control systems (ICS) — the systems that physically control energy generation and distribution.
In simple terms: this was not about stealing spreadsheets. It was about manipulating the machinery that keeps power flowing.
Affected Infrastructure: What Was Targeted
The attack hit multiple layers of Poland’s energy ecosystem.
Renewable Energy Facilities
More than 30 wind and photovoltaic farms were impacted.
What happened?
- Communication between production sites and distribution system operators (DSOs) was disrupted.
- Power generation continued.
- However, centralized visibility was impaired.
This is a textbook distributed energy systems breach scenario. Modern renewable facilities rely heavily on remote monitoring. When communications are severed, operators lose situational awareness — even if turbines continue spinning.
For North Carolina, where solar farms are rapidly expanding, this is highly relevant. Communication integrity is just as important as generation capacity.
Combined Heat and Power (CHP) Plant
At the CHP facility:
- Attackers deployed custom wiper malware targeting energy systems.
- The malware attempted to destroy operational data.
- Endpoint detection blocked the destructive payload before catastrophic damage occurred.
This is critical.
A wiper malware attack on energy systems is fundamentally different from ransomware. It aims to destroy rather than monetize.
Imagine erasing configuration data for turbines, boilers, and grid interfaces. Recovery becomes physical, not just digital.
Manufacturing Sector Company
The same malware appeared at a manufacturing site, suggesting either opportunistic lateral targeting or shared infrastructure exposure.
This underscores a key lesson:
Critical infrastructure edge device security is not confined to utilities. Manufacturing plants connected to energy systems are also at risk.
Attack Method & Tactics: How It Happened
The Poland energy sector cyber incident revealed several recurring weaknesses in OT environments.
Initial Access: Vulnerable Edge Devices
Attackers gained entry through internet-facing devices such as:
- Routers
- Firewalls
- Remote access appliances
Some reports reference FortiGate vulnerabilities exploited, suggesting that patching and firmware management were inadequate.
This is a common issue in OT networks. Edge devices are often deployed, configured once, and forgotten.
In cybersecurity terms, this was a default credentials vulnerability attack combined with poor edge hardening.
Weak Credentials and Configuration Gaps
Investigators found:
- Default or weak passwords
- Insecure remote access configurations
- Lack of proper network segmentation
These are classic operational technology security gaps.
In many energy environments, uptime takes precedence over security. Systems are left untouched because “they’re working.”
Unfortunately, attackers rely on that mindset.
Deployment of Custom Wiper Malware
Once inside, attackers deployed destructive tooling targeting:
- Remote terminal units (RTUs)
- Human machine interfaces (HMIs)
- ICS communications systems
A remote terminal unit (RTU) compromise is particularly serious. RTUs act as the bridge between physical equipment and digital control systems.
If RTUs are manipulated or destroyed, operators lose visibility and control.
The attack aimed at:
- RTU firmware corruption
- HMI data loss
- Disruption of ICS communications
This was a coordinated attempt at remote terminal units (RTUs) destruction, not data theft.
Destructive Intent, Not Extortion
Perhaps the most important takeaway:
This was not financially motivated.
There were no ransom notes.
No cryptocurrency demands.
The objective appeared to be disruption and destabilization.
That elevates this incident into the realm of strategic infrastructure targeting.
Impact & Consequences
Fortunately, there was no large-scale outage.
Energy production continued.
However, the absence of catastrophe does not equal the absence of risk.
Communication Loss
When renewable sites lose communication with central operators:
- Dispatch decisions become harder
- Grid balancing becomes riskier
- Incident response slows
This is like flying an aircraft without instruments — engines may run, but situational awareness is compromised.
What Could Have Happened?
If endpoint detection had failed at the CHP plant:
- Critical configuration data could have been erased
- Restoration might require manual system rebuilds
- Outages could cascade
In North Carolina, consider:
- Duke Energy infrastructure
- Rural electric cooperatives
- Municipal utilities
- Solar and battery storage networks
The parallels are real.
Attribution & Threat Actors
According to the CERT Polska Energy Sector Incident Report, infrastructure overlaps were identified with known energy sector threat actors, including:
- Static Tundra
- Berserk Bear
- Ghost Blizzard
- Dragonfly
Some external research suggests possible links to Sandworm-linked activity, a group previously associated with critical infrastructure attacks.
While formal attribution remains complex, one thing is clear:
These are not amateur actors.
They are known for targeting energy systems globally.
This reinforces that the Poland power grid cyberattack was not random. It fits into a pattern of energy sector probing and disruption.
Lessons Learned for North Carolina Energy and Industrial Organizations
This is where the value lies.
The Poland incident provides actionable ICS/OT incident mitigation recommendations.
- Strengthen OT/ICS Security Posture
Secure Edge Devices
- Remove unsupported devices
- Verify firmware integrity
- Disable unnecessary internet exposure
- Patch known vulnerabilities
Critical infrastructure edge device security must be treated as a frontline defense.
Eliminate Default Credentials
Replace default passwords immediately.
Implement:
- Strong password policies
- Multi-factor authentication
- Role-based access control
No RTU or firewall should ever run factory credentials.
- Improve Monitoring & Detection
Review:
- ICS logs
- Network traffic patterns
- Remote access activity
Early detection can prevent RTU compromise before destructive payloads deploy.
OT monitoring should not rely solely on traditional IT security tools.
- Incident Preparedness
Develop and rehearse:
- OT-specific cyber incident response plans
- Recovery scenarios involving firmware corruption
- Offline restoration procedures
Energy sector cyber security best practices require simulation — not just documentation.
- Collaboration and Intelligence Sharing
North Carolina organizations should actively participate in:
- Sector-specific ISACs
- State cybersecurity programs
- Federal information-sharing initiatives
Threat intelligence sharing is essential when facing sophisticated infrastructure attackers.
Broader Context: Not an Isolated Event
The Poland energy sector cyber incident echoes the 2015 Ukraine power grid hack.
In Ukraine:
- Attackers gained remote access
- Manipulated control systems
- Caused real outages
The Poland incident appears to be a modern evolution — targeting renewable infrastructure and distributed energy systems.
Globally, energy sector threat actors increasingly focus on:
- Renewable expansion
- Edge device vulnerabilities
- Distributed grid architecture
- Hybrid IT/OT environments
North Carolina, with its growing clean energy footprint, is part of this global landscape.
Why This Matters for North Carolina
North Carolina is investing heavily in:
- Solar farms
- Wind energy
- Battery storage
- Grid modernization
- Smart grid deployments
These technologies depend on:
- Remote terminal units
- Industrial control systems
- Edge networking equipment
The same architectural patterns seen in Poland exist here.
A Poland renewable energy cyberattack may feel geographically distant — but the technical vulnerabilities are universal.
Final Thoughts: Resilience Over Reaction
The Poland energy sector cyber incident is not just another headline.
It is a warning.
It demonstrates that:
- OT/ICS cybersecurity cannot be secondary.
- Edge device security is critical.
- Default credentials remain a persistent risk.
- Destructive attacks are a real threat to energy infrastructure.
For North Carolina energy providers, manufacturers, and infrastructure operators, the path forward is clear:
Invest in proactive defense.
Audit edge exposure.
Segment OT networks.
Rehearse response.
Share intelligence.
Because in critical infrastructure, resilience is not optional.
It is foundational.
FAQs:
- What was the Poland energy sector cyber incident?
The Poland energy sector cyber incident was a coordinated December 29, 2025 cyberattack targeting renewable energy farms, a combined heat and power plant, and a manufacturing company. The attack focused on operational technology (OT) and industrial control systems (ICS), using destructive malware rather than ransomware.
- Was the Poland power grid cyberattack a ransomware attack?
No. Unlike typical ransomware attacks, the Poland power grid cyberattack involved custom wiper malware designed to destroy operational data and disrupt ICS communications, not extort money.
- How did attackers gain access during the Poland renewable energy cyberattack?
Initial access was achieved through vulnerable internet-facing edge devices such as routers and firewalls. Weak configurations and default credentials played a significant role in the compromise.
- What systems were targeted in the OT/ICS cybersecurity incident in Poland?
The attackers targeted:
- Remote terminal units (RTUs)
- Human machine interfaces (HMIs)
- Industrial control system communications
- Renewable energy site monitoring infrastructure
- Did the Poland critical infrastructure cyber incident cause power outages?
No major outages occurred. While communication between renewable facilities and distribution operators was disrupted, power generation continued.
- What is a wiper malware attack on energy systems?
A wiper malware attack is designed to permanently destroy system data or firmware rather than encrypt it for ransom. In energy systems, this can lead to RTU destruction, HMI data loss, and severe operational disruption.
- Why is this incident important for North Carolina energy providers?
North Carolina’s growing renewable and distributed energy infrastructure relies heavily on OT and ICS technologies similar to those targeted in Poland. The incident highlights the need for stronger edge device security, monitoring, and OT-specific incident response planning.
- What are the key cybersecurity lessons from the CERT Polska Energy Sector Incident Report?
Key lessons include:
- Remove default credentials immediately
- Harden internet-facing edge devices
- Monitor ICS logs and network traffic
- Segment OT and IT networks
- Develop OT-specific cyber incident response plans
- Which threat actors were linked to the Poland energy sector cyber attack?
CERT Polska identified infrastructure overlaps with known energy sector threat clusters such as Static Tundra, Berserk Bear, Ghost Blizzard, and Dragonfly. Some analyses suggest possible Sandworm-linked activity.
- How can utilities protect against similar OT/ICS attacks?
Energy organizations should:
- Patch and secure edge devices
- Enforce strong authentication policies
- Implement network segmentation
- Deploy OT-aware monitoring tools
- Participate in threat intelligence sharing programs