Malaysia Airlines Ransomware Attack: What North Carolina Businesses Should Know About the Qilin Ransomware Claim
In late February 2026, cybersecurity monitoring platforms began reporting that Malaysia Airlines had been listed on the dark web leak site of the Qilin ransomware group. Within hours, headlines referencing a potential Malaysia Airlines ransomware attack began circulating across global tech media.
For businesses and travelers in North Carolina — particularly those who rely on aviation, logistics, or global partnerships — the story is more than international cybersecurity news. It is a reminder of how quickly a ransomware claim can disrupt trust, raise public concern, and expose the fragile digital backbone of critical industries.
But here’s the key distinction: as of now, this is a ransomware claim — not a confirmed breach.
In this article, we will break down:
- What actually happened
- Who the Qilin ransomware group is
- The difference between a ransomware claim and a verified data breach
- What kind of data could hypothetically be at risk
- Why airlines are frequent ransomware targets
- And what North Carolina businesses can learn from this situation
What Happened: The Qilin Ransomware Claim Against Malaysia Airlines
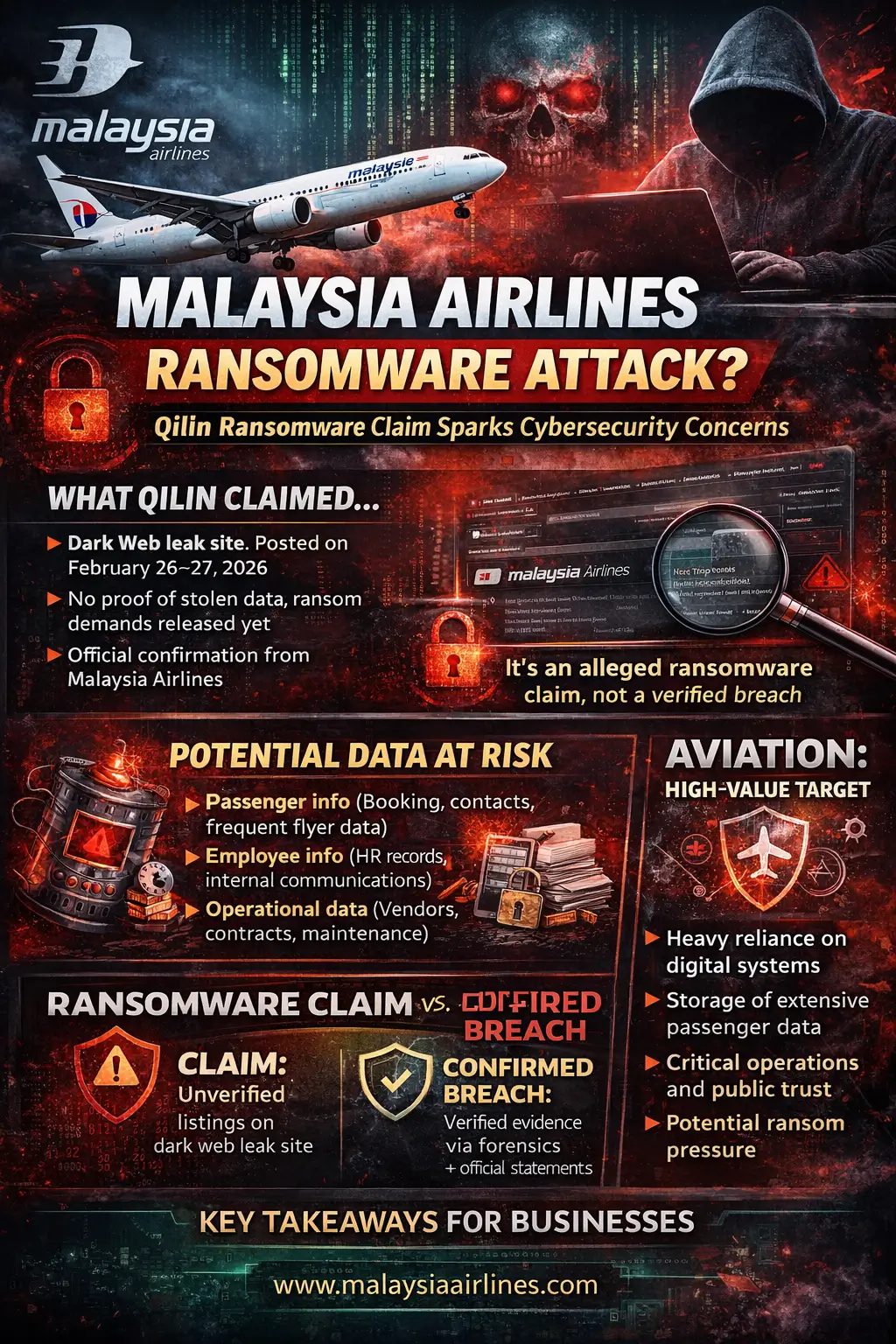
Between February 26–27, 2026, the Qilin ransomware group listed Malaysia Airlines on its dark web victim site, a page commonly used by ransomware gangs to publicly name organizations they claim to have breached.
At the time of writing:
- No data samples have been released publicly
- No proof of system compromise has been published
- No ransom demand amount has been disclosed
- Malaysia Airlines has not officially confirmed a breach
- Cybersecurity authorities have not verified the claim
This matters.
In ransomware reporting, especially in the early days of a listing, it is common for threat actors to publish only the name of an organization. Sometimes this listing precedes negotiations. In other cases, it is used as pressure to encourage payment.
📌 What this means: At this stage, the “Malaysia Airlines ransomware attack” remains an alleged cyber-attack — not a verified airline data breach ransomware event.
For North Carolina readers, think of this like a public accusation without evidence presented in court. The name appears, but the details have not yet been proven.
Who Is Qilin Ransomware?
What Is Qilin Ransomware?
Qilin is a ransomware group that emerged in 2022 and operates under a Ransomware-as-a-Service (RaaS) model.
Under this model:
- Core developers create the ransomware software.
- Affiliates (independent cybercriminal operators) deploy it against victims.
- Profits from ransom payments are shared.
This structure allows ransomware gangs to scale rapidly — much like a franchise business model, except the product is cyber extortion.
How Qilin Operates
Qilin is known for using double-extortion ransomware tactics, which include:
- Encrypting an organization’s systems
- Stealing sensitive data
- Threatening to publish the stolen data if ransom is not paid
This tactic increases pressure. Even if a company has backups and can restore systems, the threat of public data exposure creates reputational and regulatory risk.
Qilin has previously targeted:
- Healthcare institutions
- Financial services firms
- Manufacturing companies
- Transportation and logistics providers
Its presence in the aviation sector, if confirmed, would not be unusual. Airlines are data-heavy operations — and ransomware groups follow data.
Scope of the Claim: What Is — and Isn’t — Known
One of the most important elements in responsible ransomware reporting is understanding the difference between:
- A listing on a dark web leak site
- A confirmed breach backed by forensic evidence
In the Malaysia Airlines case:
- The leak page reportedly includes only the organization’s name.
- No screenshots of internal systems have surfaced.
- No stolen files have been previewed.
- No technical details of the alleged intrusion have been shared.
Cyber threat intelligence analysts often caution that early listings may serve as negotiation tactics. In some cases, names are posted before ransomware deployment is fully validated or before discussions conclude.
That doesn’t mean the claim is false. It means verification takes time.
📌 Ransomware claim vs confirmation is a crucial distinction. Responsible businesses — and responsible media — wait for corroborated evidence before labeling something a confirmed Malaysia Airlines cyber-attack.
What Kind of Data Could Be at Risk?
If — hypothetically — Qilin did access Malaysia Airlines’ systems, what types of data might be exposed?
While there is no evidence of compromise yet, typical airline ransomware scenarios involve:
Passenger Information
- Booking details
- Contact information
- Frequent flyer program data
- Travel history
- Payment-related metadata
This creates potential airline passenger data risk.
Employee Data
- HR records
- Payroll information
- Internal communications
- Credential data
Operational Systems
- Vendor contracts
- Maintenance documentation
- Internal scheduling systems
- Supply chain coordination data
Sensitive Business Documents
- Strategic plans
- Financial records
- Legal agreements
For North Carolina businesses operating in transportation, healthcare, finance, or retail, this should feel familiar. The data categories airlines manage are similar to those in many mid-sized and enterprise organizations.
The difference is scale — and public visibility.
Why Aviation Is a Prime Target for Ransomware
The aviation sector has increasingly become a focal point for cybersecurity threats in aviation due to several structural realities:
- Heavy Digital Dependency
Modern airlines depend on:
- Online booking systems
- Cloud infrastructure
- Aircraft maintenance software
- Real-time scheduling platforms
- Global vendor integrations
Disrupt one piece, and ripple effects can cascade across continents.
- High-Value Data
Airlines store:
- Personally identifiable information (PII)
- Payment data
- Passport details
- Travel histories
That data is valuable on underground markets.
- Time Sensitivity
Unlike some industries, airlines cannot “pause operations” without severe financial and reputational consequences. Ransomware gangs understand that downtime equals pressure.
For businesses in North Carolina — especially those near Raleigh-Durham International Airport (RDU) or operating logistics hubs — this mirrors local reality. Critical infrastructure environments are always high-value targets.
Why Verification Matters in Ransomware Reporting
In the era of social media threat intelligence, news spreads faster than confirmation.
A dark web screenshot can circulate globally within minutes. But cybersecurity verification involves:
- Log analysis
- Endpoint detection review
- Network forensics
- Threat intelligence correlation
- Official organizational statements
Many ransomware claims ultimately prove exaggerated, misattributed, or strategically timed.
For North Carolina business leaders, this distinction is critical. If your company were listed on a ransomware site tomorrow, the first steps would include:
- Activating incident response teams
- Engaging forensic specialists
- Preserving logs
- Assessing scope
- Communicating responsibly
Not immediately assuming total compromise.
Lessons for North Carolina Businesses and Travelers
Even though the Malaysia Airlines alleged data breach remains unverified, the broader implications are clear.
Lesson 1: Double-Extortion Is the New Normal
Ransomware is no longer just about encryption. Data theft is now standard.
Organizations must assume:
- Attackers may exfiltrate data
- Reputation risk may exceed operational risk
Lesson 2: Backups Are Necessary — But Not Enough
Backups help restore systems.
They do not prevent data publication threats.
Businesses must invest in:
- Data loss prevention (DLP)
- Endpoint detection and response (EDR)
- 24/7 monitoring
- Network segmentation
Lesson 3: Incident Response Plans Must Be Current
When was the last time your organization tested its ransomware response?
A well-documented incident response plan should include:
- Internal communication protocols
- Legal counsel contacts
- Cyber insurance coordination
- Public relations strategy
- Regulatory notification procedures
Lesson 4: Customer Trust Is Fragile
Airlines trade on trust.
So do banks, hospitals, and managed IT providers.
Even an unverified ransomware claim can:
- Impact stock prices
- Trigger customer concern
- Invite regulatory scrutiny
- Create social media backlash
Trust, once shaken, takes years to rebuild.
The Bigger Picture: Ransomware’s Expanding Threat Landscape
Whether or not the Malaysia Airlines cyber-attack claim proves accurate, the trend is undeniable.
Ransomware is evolving in three critical ways:
- Industrialization
Ransomware-as-a-Service has lowered barriers to entry for cybercriminals.
- Target Expansion
No sector is off-limits:
- Aviation
- Healthcare
- Municipal governments
- Universities
- Manufacturing
- Psychological Pressure
Public leak sites create a reputational countdown clock.
For North Carolina businesses — from Charlotte financial institutions to Raleigh tech firms — the lesson is clear: cybersecurity is no longer optional overhead. It is operational infrastructure.
Conclusion: Why This Story Matters Beyond Malaysia
At the time of writing, the Malaysia Airlines ransomware attack remains an unverified claim by the Qilin ransomware group. No confirmed breach details have been released.
But the story matters.
It illustrates:
- The speed of modern ransomware reporting
- The power of dark web leak sites
- The increasing use of double-extortion tactics
- The importance of distinguishing claim from confirmation
- The reputational risks organizations face in today’s threat environment
For North Carolina organizations, the takeaway is not fear — it is preparation.
Proactive cybersecurity defenses, tested incident response plans, and ongoing threat intelligence monitoring are no longer advanced strategies. They are baseline requirements.
In a world where a company’s name can appear on a ransomware site overnight, readiness is the difference between disruption and resilience.
And that is a lesson no business — airline or otherwise — can afford to ignore.
Frequently Asked Questions (FAQs)
Malaysia Airlines Ransomware Attack & Qilin Ransomware Claim
- Has Malaysia Airlines confirmed a ransomware attack?
As of now, Malaysia Airlines has not officially confirmed a ransomware attack. The Qilin ransomware group listed the airline on its dark web leak site in late February 2026, but no verified evidence or public confirmation has been released. This means the situation remains an alleged ransomware claim, not a confirmed breach.
- What is the “Qilin ransomware claim” involving Malaysia Airlines?
The Qilin ransomware claim refers to the group publicly listing Malaysia Airlines on its leak site, which is commonly used by ransomware gangs to pressure victims into paying ransom. However, no proof of stolen data, ransom demand, or system compromise has been publicly shared so far.
- What is Qilin ransomware?
Qilin is a ransomware group that has been active since 2022. It operates under a Ransomware-as-a-Service (RaaS) model, meaning developers create the malware and affiliates deploy it against victims. Qilin is known for using double-extortion tactics, where attackers both encrypt systems and threaten to publish stolen data if a ransom is not paid.
- What is double-extortion ransomware?
Double-extortion ransomware is a tactic where cybercriminals:
- Encrypt a company’s systems, and
- Steal sensitive data before encryption, threatening to publish it publicly if payment is not made.
This method increases pressure on organizations because even if they can restore systems from backups, they still face potential reputational and legal consequences from data exposure.
- What kind of data could be at risk in an airline ransomware attack?
If a breach were confirmed (which has not happened in this case), potentially exposed data could include:
- Passenger booking and contact details
- Frequent flyer information
- Employee records
- Vendor and operational data
- Internal business documents
Airlines manage large volumes of personal and operational data, making them attractive targets for ransomware gangs.
- Why are airlines frequently targeted by ransomware groups?
Airlines are considered high-value targets because:
- They rely heavily on digital systems
- They store large amounts of sensitive passenger data
- Operational disruptions can cause significant financial losses
- Public trust is critical to their business
Cybercriminals often target industries where downtime and reputational damage create strong pressure to pay ransom demands.
- Does a dark web listing automatically mean a confirmed data breach?
No. A listing on a ransomware group’s leak site does not automatically confirm that a breach has occurred. Sometimes threat actors publish a company’s name before releasing proof, and in certain cases, listings are part of negotiation tactics. Verification requires forensic investigation and official confirmation.
- How do cybersecurity teams verify ransomware claims?
Cybersecurity professionals rely on:
- Digital forensics and log analysis
- Endpoint and network monitoring tools
- Threat intelligence feeds
- Official company statements
- Regulatory disclosures
Only after technical evidence is analyzed can a ransomware claim be confirmed as a legitimate breach.
- Should travelers be concerned about their data?
At this stage, there is no confirmed evidence that passenger data has been compromised. Travelers should continue practicing general cybersecurity awareness, such as:
- Monitoring financial accounts
- Using strong, unique passwords
- Enabling multi-factor authentication (MFA)
If an airline confirms a breach, affected customers are typically notified with guidance on next steps.
- What can North Carolina businesses learn from the Malaysia Airlines ransomware claim?
The key lessons include:
- Have a tested incident response plan in place
- Invest in proactive cybersecurity defenses
- Monitor for data exfiltration, not just system encryption
- Understand the difference between ransomware claims and verified breaches
- Prepare communication strategies for potential cyber incidents
Whether in aviation, healthcare, finance, or manufacturing, businesses in North Carolina face similar ransomware risks.
- What is the difference between a ransomware claim and a confirmed cyber-attack?
A ransomware claim is when a threat actor publicly asserts that they have breached an organization. A confirmed cyber-attack occurs only after forensic evidence verifies unauthorized access, data theft, or system compromise. Media coverage may begin at the claim stage, but confirmation requires investigation.
- How can organizations protect themselves from ransomware threats like Qilin?
Organizations should implement:
- Multi-factor authentication (MFA)
- Regular data backups (offline and immutable)
- Endpoint detection and response (EDR)
- Network segmentation
- Employee cybersecurity training
- Ongoing vulnerability patching
- 24/7 security monitoring
Ransomware prevention requires layered defenses rather than a single security tool.

